Avoid Coronavirus Phishing Scams Stay Safe Online
Avoid coronavirus phishing scams is crucial in today’s digital world. These scams prey on people’s anxieties about the virus, using deceptive emails, texts, and websites to trick you into revealing personal information. Understanding the tactics used in these scams is the first step to protecting yourself.
This post delves into the various types of coronavirus-related phishing scams, from fake charities to fraudulent health updates. We’ll examine the common characteristics, red flags, and preventative measures to help you spot and avoid these malicious attempts. Learning how to verify information and report suspicious activity is essential in protecting yourself and your loved ones from these harmful scams.
Understanding Coronavirus Phishing Scams
Coronavirus-related phishing scams are a serious threat, exploiting people’s fear and anxiety about the pandemic to steal personal information. These scams take advantage of the heightened public awareness and the constant flow of information related to the virus. Criminals are quick to adapt, using new information and current events to create convincing and malicious content. It is crucial to understand the common characteristics of these scams to protect yourself and your loved ones.Coronavirus phishing scams rely heavily on emotional manipulation.
They leverage people’s worry about the virus and their desire to stay informed, creating a sense of urgency that encourages hasty actions. This urgency often overrides critical thinking, making individuals more susceptible to fraudulent attempts.
Common Characteristics of Coronavirus Phishing Scams
These scams often mimic legitimate organizations, using official-looking logos and language to build trust. They create a sense of urgency and exploit people’s fear and anxiety about the virus. Phishing scams can appear in various forms, including emails, text messages, and websites.
Examples of Coronavirus Phishing Tactics
Various methods are employed to trick individuals into revealing personal information. These tactics include creating fake charities, impersonating health organizations, or using spoofed websites to mimic legitimate platforms.
- Fake Charities: These scams often claim to be raising funds for coronavirus relief efforts. They may use emotionally charged language and a sense of urgency to pressure victims into donating. These requests are often delivered via email, text message, or social media. They may claim to be associated with reputable organizations, but the links and contact information are often fraudulent.
- Fake Health Updates: These scams attempt to exploit people’s desire for accurate information about the virus. They may send emails or text messages claiming to provide updates on treatments, cures, or vaccine availability. These updates are often laced with misinformation or malicious links. They often include scare tactics and promises of exclusive information, tempting individuals to click on suspicious links.
- Fake Government or Health Organization Websites: These scams create websites that mimic legitimate government or health organization websites. They often ask for personal information, such as login credentials or financial details. These websites usually have slightly altered URLs or a different domain name to avoid suspicion.
Methods Used to Trick Individuals
Criminals use various techniques to deceive victims. These tactics include creating a sense of urgency, exploiting fear, and using official-looking logos and language to build trust.
- Creating a Sense of Urgency: Scammers often use time-sensitive language, suggesting that immediate action is required. This pressure discourages critical thinking and encourages impulsive decisions.
- Exploiting Fear and Anxiety: By highlighting the dangers of the virus, scammers prey on people’s anxieties and fears. This creates a sense of vulnerability and encourages hasty responses.
- Using Official-Looking Logos and Language: Criminals mimic the design and language of legitimate organizations. This creates an aura of credibility and increases the likelihood of individuals falling for the scam.
Comparison of Coronavirus Phishing Scams
The following table compares different types of coronavirus phishing scams, highlighting their characteristics and methods.
| Type of Scam | Characteristics | Methods |
|---|---|---|
| Fake Charities | Claim to be raising funds for coronavirus relief. | Use emotionally charged language, create a sense of urgency, and pressure victims into donating. |
| Fake Health Updates | Attempt to exploit people’s desire for accurate information about the virus. | Send emails or text messages with misinformation or malicious links. Often include scare tactics and promises of exclusive information. |
| Fake Government/Health Websites | Mimic legitimate government or health organization websites. | Ask for personal information, such as login credentials or financial details. Often use slightly altered URLs or different domain names. |
Recognizing the Signs of a Coronavirus Phishing Scam
Coronavirus phishing scams are a serious threat, exploiting the fear and uncertainty surrounding the pandemic. These scams attempt to trick you into revealing sensitive information, often for financial gain. Understanding the common red flags is crucial for protecting yourself and your loved ones.Phishing scams often use urgency and a sense of crisis to manipulate victims. They rely on creating a false sense of panic or importance, aiming to pressure you into acting quickly without thinking critically.
This makes recognizing the subtle signs of a scam even more important. Critically evaluating the source, content, and context of communications is vital.
Identifying Key Red Flags
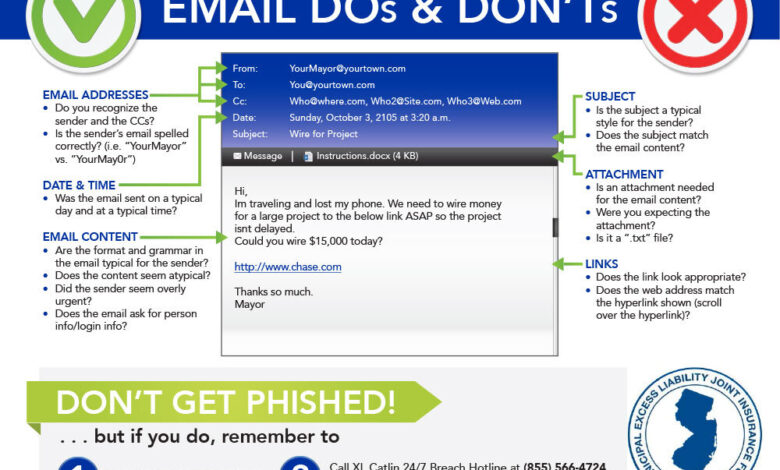
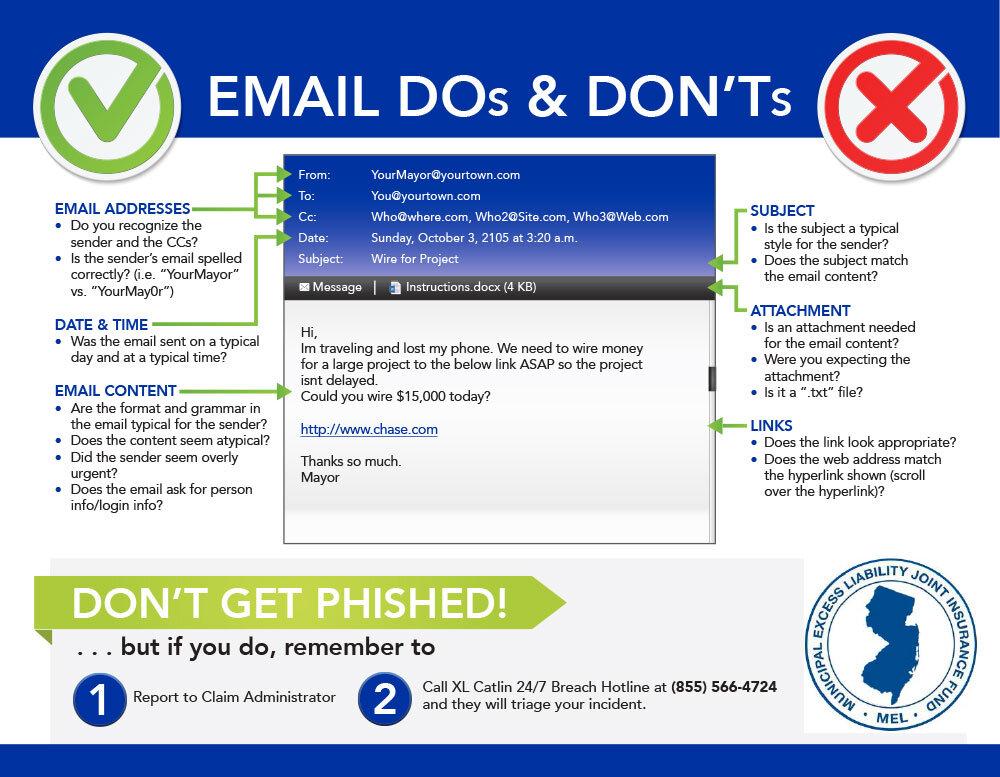
Recognizing the key red flags is essential to avoid falling prey to coronavirus phishing scams. These red flags often appear in emails, text messages, or social media posts, and can be subtle. Critically examining the source and content of communications is vital.
- Suspicious Email Addresses: Phishing emails often use email addresses that are slightly altered or look similar to legitimate organizations. Pay close attention to the email address; check for misspellings or subtle differences from the official address.
- Suspicious Links: Hover your mouse over links before clicking. Look closely at the URL. Shortened URLs or URLs with unusual domains are often used to mask the true destination. Be wary of links that lead to unfamiliar websites or sites that don’t match the context of the email.
- Suspicious Attachments: Avoid opening attachments from unknown senders, especially those related to coronavirus. Malware or viruses can be hidden within these files. Be cautious even if the attachment appears to be from a trusted source; verify the sender directly.
- Urgent Tone and Requests for Personal Information: Phishing scams frequently employ an urgent tone, demanding immediate action. They often request personal information like passwords, credit card details, or social security numbers under false pretenses. Never provide sensitive information in response to an email or message that seems urgent or demanding.
- Generic Greetings: Phishing scams frequently use generic greetings such as “Dear User” or “Dear Customer” instead of your name. This is a strong indicator that the message is not personalized and may be a scam.
Examples of Grammatical Errors and Urgent Tones
Phishing scams often contain grammatical errors, typos, and poor sentence structure. These inconsistencies can be clues to their fraudulent nature.
- Example of Grammatical Errors: “We need you to update your account immediately. Please click this link to complete the process.” (Notice the abrupt phrasing and potential grammatical errors).
- Example of Urgent Tones: “Urgent! Your Coronavirus Relief Package is Ready! Claim Your Funds Now!” (The use of the word “urgent” and the direct request for immediate action are strong indicators of a scam).
Common Phishing Scam Tactics
A table outlining common phishing scam tactics and their red flags helps to identify potential threats.
| Phishing Scam Tactics | Red Flags |
|---|---|
| Fake Government Agencies | Urgent requests for personal information, generic greetings, suspicious links and attachments, grammatical errors. |
| Fake Charities | Requests for donations with links, generic greetings, urgent tones, suspicious links. |
| Fake Healthcare Providers | Urgent requests for health information, generic greetings, suspicious links and attachments, grammatical errors. |
| Fake Delivery Services | Urgent requests for payment information, suspicious links, generic greetings, grammatical errors. |
Protecting Yourself from Coronavirus Phishing Scams

Staying safe online during a pandemic requires vigilance. Phishing scams related to the coronavirus exploit public concern and fear to trick people into revealing sensitive information. This proactive approach focuses on recognizing and preventing these scams.Knowing how to identify and avoid these scams is critical for safeguarding your personal data and financial well-being. These scams often use urgent language and fake authority figures to manipulate you.
By understanding the tactics and adopting strong security practices, you can effectively protect yourself.
Verifying Information Authenticity
Authenticating information is essential in combating misinformation. Reliable sources, like official government websites, reputable news organizations, and health organizations (e.g., the CDC, WHO), are crucial for verifying information about the coronavirus. Always check the source’s legitimacy and look for verifiable details, such as contact information and credentials. Cross-reference information from multiple trusted sources to build a comprehensive understanding.
Responding to Suspicious Emails and Texts
When encountering suspicious emails or text messages related to the coronavirus, adopt a cautious approach. Never click on links or open attachments from unknown senders. Instead, contact the organization or individual mentioned in the message through a verified and trusted channel (e.g., directly contacting the bank or organization). If the message seems urgent or contains threats, report it immediately to the relevant authorities.
Reporting Suspicious Emails and Websites
Reporting suspicious emails and websites is critical to preventing the spread of these scams. Use your email provider’s reporting mechanisms or contact the website’s administrators directly. Providing detailed information about the scam, including the sender’s email address or website URL, can help authorities track and investigate these fraudulent activities. Many organizations have dedicated email addresses for reporting suspicious activity.
Importance of Strong Passwords and Multi-Factor Authentication
Strong passwords and multi-factor authentication (MFA) are essential security measures. Use a unique and complex password for each online account. Avoid using easily guessable information like birthdays or names. Enabling MFA adds an extra layer of security, requiring a second verification step (e.g., a code sent to your phone) to access your account. This prevents unauthorized access even if a password is compromised.
Cybersecurity Awareness Training
Regular cybersecurity awareness training plays a vital role in preventing phishing scams. These trainings can educate individuals about common phishing techniques, warning signs, and best practices for protecting personal data. They empower individuals to recognize and avoid potentially harmful situations. Training should be ongoing to keep up with evolving tactics.
Securing Online Accounts
Securing online accounts involves a multi-step approach. First, ensure all software is updated to the latest versions, which often include security patches. Second, use strong passwords and enable MFA. Third, monitor your account activity regularly for any suspicious transactions. Fourth, regularly review privacy settings and adjust them as needed.
Finally, be cautious about sharing personal information online and avoid clicking on unknown links.
Examples of Safe Practices
Staying safe online during a pandemic requires vigilance and critical thinking. Phishing scams, often disguised as urgent coronavirus-related alerts, are designed to trick you into revealing sensitive information. Understanding these tactics and practicing safe online habits is crucial to protect yourself and your loved ones.
Real-World Examples of Coronavirus Phishing Scams
Numerous scams have targeted individuals during the pandemic, exploiting fear and uncertainty surrounding COVID-19. One common tactic involved fake websites mimicking official government health organizations. These sites requested personal information, including banking details, in exchange for supposedly vital health information or cures. Another prevalent type involved emails claiming to offer free COVID-19 testing or vaccinations. Clicking on malicious links in these emails could lead to malware infections.
Consequences of Falling Victim to These Scams
The consequences of falling prey to coronavirus phishing scams can be severe. Financial losses are a major concern, as victims may be directed to fraudulent websites designed to steal banking credentials. Beyond financial implications, personal data breaches can lead to identity theft, impacting creditworthiness and causing significant stress. Malware infections can compromise personal devices, leading to data loss and further financial harm.
Check cima ethics confidentiality rules to inspect complete evaluations and testimonials from users.
Legitimate Resources for Coronavirus Information
Reliable sources for coronavirus information are essential for staying informed without falling victim to scams. Government health agencies, such as the Centers for Disease Control and Prevention (CDC) in the United States, or similar organizations in other countries, are the primary sources for trustworthy information. Reputable news outlets, verified by their journalistic standards and fact-checking practices, provide essential context and updates.
Scientific journals and publications dedicated to medical research can provide further insights into the pandemic’s evolution.
Comparing Reliable Sources with Common Scams
| Reliable Source | Common Scam |
|---|---|
| Official Government Health Agencies (e.g., CDC, WHO) | Fake websites mimicking government agencies, requesting personal information |
| Reputable News Outlets (with verifiable sources) | Emails or social media posts with sensationalized or misleading claims |
| Peer-Reviewed Medical Journals | Offers for unproven cures or treatments |
| Trusted Educational Institutions | Links to fake research or studies |
Verifying Information from Official Government Agencies
Verifying information from official government agencies is crucial to avoid scams. Always check the agency’s official website for announcements and guidelines. Look for a secure website with a valid domain name and a proper contact page. Verify the sender’s email address or phone number. Contact the agency directly to confirm any information you are unsure about.
Don’t rely solely on social media posts or unofficial websites.
Elaborating on Prevention Strategies
Staying safe online during a pandemic requires more than just awareness; it demands proactive measures. Phishing scams are constantly evolving, employing sophisticated tactics to trick even the most cautious users. This section dives into advanced prevention strategies, focusing on critical evaluation of online information, software updates, and responsible online behavior.
Critical Evaluation of Online Information
Identifying credible sources is crucial in the fight against misinformation. Phishing scams often rely on creating a sense of urgency or fear to manipulate victims. Always scrutinize the source of any information, especially if it involves sensitive personal data or financial transactions. Look for verified credentials, professional-looking design, and a clear contact information.
Importance of Keeping Software Updated
Cybersecurity threats are constantly evolving. Software updates often include crucial security patches that address vulnerabilities exploited by scammers. Outdated software leaves your devices vulnerable to attacks, making it easier for malicious actors to gain access to your information.
Significance of Not Clicking on Suspicious Links or Attachments
Never click on links or open attachments from unknown senders, even if they appear to be from a trusted source. Hovering over links to see the actual destination URL before clicking can help you identify potential scams. Similarly, be wary of unusual requests for personal information, especially those that create a sense of urgency.
Comparison of Phishing Scams and Legitimate Communication Methods
| Characteristic | Phishing Scam | Legitimate Communication |
|---|---|---|
| Sender | Unknown or spoofed sender (pretending to be from a known source) | Known and verified sender (official company, government agency, etc.) |
| Content | Urgent requests for personal information, threats, or promises of rewards | Clear and professional language, providing information or requesting specific actions |
| Links/Attachments | Suspicious or shortened links, malicious attachments | Clear and verified links, legitimate attachments |
| Tone | Intimidating, urgent, or overly enthusiastic | Professional and respectful |
| Grammar/Spelling | Errors in grammar and spelling | Professional and correct grammar and spelling |
| Request | Unusual requests for personal information or money | Standard requests for information within the context of a relationship |
Strategies for Reporting and Recovery
Protecting yourself from coronavirus phishing scams goes beyond recognizing the signs. Equally crucial is knowing how to respond when you suspect you’ve been a victim. This section Artikels the process for reporting scams and recovering from compromised accounts, with a focus on regaining control and minimizing potential damage.
Reporting Coronavirus Phishing Scams, Avoid coronavirus phishing scams
Reporting phishing scams is vital for preventing further harm to others. It allows authorities to track and analyze trends, identify perpetrators, and implement preventative measures. Accurate reporting also helps in gathering evidence for potential legal actions.
- Contact your financial institution immediately if you suspect a fraudulent transaction.
- Report the phishing attempt to the Federal Trade Commission (FTC) through their website or by phone. Detailed information about the scam, including the website address, emails, and any suspicious links, is crucial for the investigation.
- If the scam involves a government agency or website, report it to the appropriate government body. For example, if the scam mimics the IRS, report it to the IRS.
Recovering from a Compromised Account
Immediate action is critical to minimizing damage when an account is compromised. Delay can lead to significant financial losses and identity theft.
- Change Passwords: Immediately change the passwords for all accounts, especially those linked to the compromised account. Use strong, unique passwords for each account, and enable two-factor authentication wherever possible. Using a password manager can aid in generating and storing strong passwords for different accounts.
- Monitor Accounts: Actively monitor your accounts for suspicious activity. Set up alerts for unusual transactions, login attempts, and other potentially fraudulent actions. Regularly check your account statements for discrepancies. This proactive monitoring can prevent further loss and help you detect any unusual transactions or activity immediately.
- Contact Financial Institutions: If your bank account is compromised, contact your bank immediately. Provide them with details about the fraudulent transactions and request a freeze on your account to prevent further unauthorized access.
Examples of Bank Account Compromise Recovery
The steps for recovering a compromised bank account mirror the broader recovery process. Immediately contacting your bank is paramount.
- Report Suspicious Activity: Report any unauthorized transactions or access attempts to your bank immediately. Provide detailed information, including dates, times, transaction amounts, and descriptions. The sooner you report the activity, the better the chances of stopping further fraudulent activity and preventing the loss of funds.
- Account Freeze: Request a freeze on your account to prevent further unauthorized access. This measure temporarily blocks all transactions until you can resolve the issue.
- Identity Theft Protection: Contact the Federal Trade Commission (FTC) and request a fraud alert to protect your identity from further theft. This alert can be applied to your credit reports and helps to detect any fraudulent activity associated with your personal information.
Importance of Immediately Changing Passwords
Changing passwords promptly is essential to mitigate the risk of further damage. This is especially critical when a password has been compromised in a phishing attack.
Immediate password changes can prevent further unauthorized access to accounts and stop criminals from using your information for malicious purposes.
Steps to Take When Personal Information is Stolen
Stolen personal information can lead to various issues, including financial fraud, identity theft, and other serious consequences.
- Report to Authorities: Report the theft of your personal information to the relevant authorities, such as the FTC and your local law enforcement agency. Filing a report is a crucial step in the process of recovering from identity theft.
- Monitor Credit Reports: Monitor your credit reports regularly to detect any fraudulent activity. Request a free copy of your credit report from each of the three major credit bureaus—Equifax, Experian, and TransUnion—at least once a year.
- Place Fraud Alerts: Place fraud alerts on your credit reports to prevent unauthorized accounts or applications from being opened in your name. This measure can help protect your creditworthiness and prevent further identity theft.
Concluding Remarks: Avoid Coronavirus Phishing Scams
In conclusion, staying vigilant and informed is key to avoiding coronavirus phishing scams. By understanding the common tactics, recognizing the red flags, and implementing strong security practices, you can protect yourself from these dangerous attempts. Remember to always verify information, be cautious of urgent requests, and report any suspicious activity immediately. By following these guidelines, you can significantly reduce your risk of falling victim to a scam and maintain your online safety.