Data Security Risks for Finance Teams A Deep Dive
Data security risks for finance teams are a critical concern in today’s digital landscape. Financial institutions handle vast amounts of sensitive data, making them prime targets for cyberattacks. Protecting this information is not just about preventing breaches; it’s about safeguarding reputations, maintaining customer trust, and avoiding substantial financial losses. This in-depth exploration delves into the various threats, vulnerabilities, and crucial steps financial teams can take to mitigate risks.
From phishing scams to sophisticated insider threats, the landscape of cyberattacks is constantly evolving. This comprehensive guide will cover the crucial aspects of data security, including regulatory compliance, building a strong security culture, and adopting emerging technologies. Understanding these risks and implementing proactive measures are essential for the long-term health and stability of any financial organization.
Introduction to Data Security Risks for Finance Teams
Data security is paramount in the financial sector, where sensitive customer information, financial transactions, and institutional records are at constant risk. Protecting this data is not just a best practice; it’s a critical necessity for maintaining trust, preventing financial losses, and upholding the integrity of financial institutions. A data breach can have catastrophic consequences, impacting not only the institution’s bottom line but also its reputation and the confidence of its clients.Financial institutions are the custodians of vast amounts of sensitive data, making them prime targets for cybercriminals.
Protecting this data is not just about implementing robust security measures; it’s about understanding the vulnerabilities specific to each type of institution and proactively mitigating those risks. The consequences of a breach can range from substantial financial penalties to irreparable damage to the institution’s reputation.
Significance of Data Security in Finance
Data security is critical in finance due to the high value and sensitivity of the information handled. Financial institutions process and store confidential customer details, transaction records, and internal strategies. Breaches expose sensitive information, leading to financial losses, reputational damage, and regulatory penalties. Protecting this data safeguards the financial well-being of both the institution and its clients.
Robust security measures are essential for maintaining trust and stability in the financial ecosystem.
Critical Role of Data Protection for Financial Institutions
Data protection is fundamental to the survival and success of financial institutions. A strong data security posture builds trust among clients, investors, and regulators. It minimizes the risk of financial losses and reputational damage, ensuring the institution’s continued operations and financial health. Proactive data protection measures are crucial to preventing breaches and minimizing the impact should a breach occur.
This includes employing strong authentication methods, regular security audits, and staff training programs.
Potential Financial and Reputational Consequences of Data Breaches
The consequences of a data breach can be severe and far-reaching. Financial institutions face potential fines, lawsuits, and loss of investor confidence. Reputational damage can be long-lasting, impacting customer loyalty and trust. Financial losses include direct costs associated with incident response, legal fees, and compensation to affected customers. The indirect costs, such as loss of revenue and market share, can be even more significant.
Examples include the 2017 Equifax breach, which cost the company billions of dollars and severely damaged its reputation.
Key Stakeholders Affected by Data Security Risks in Finance
Data security risks affect various stakeholders within and outside financial institutions. Customers, investors, regulatory bodies, and the institution itself are all susceptible to negative consequences from breaches. Customers face identity theft, financial fraud, and loss of trust in the institution. Investors may lose confidence in the institution’s ability to protect their investments. Regulatory bodies may impose significant fines or sanctions.
The institution itself faces financial losses, operational disruption, and reputational damage.
Data Security Vulnerabilities Across Financial Institutions
Different types of financial institutions face varying data security vulnerabilities. These vulnerabilities are often shaped by the specific nature of their operations, the volume of sensitive data handled, and the complexity of their systems. A comprehensive understanding of these vulnerabilities is essential for implementing targeted security measures.
| Institution Type | Key Data Security Vulnerabilities | Examples of Threats | Mitigation Strategies |
|---|---|---|---|
| Banks | Phishing attacks, malware infections, insider threats, weak authentication protocols. | Social engineering tactics, targeted ransomware attacks, skimming of ATM cards. | Multi-factor authentication, strong passwords, regular security awareness training, robust network security. |
| Investment Firms | Unauthorized access to trading systems, insider trading, market manipulation, data breaches. | Sophisticated hacking attempts, social engineering, malware infections, and data theft from servers. | Enhanced access controls, encryption of sensitive data, robust cybersecurity infrastructure, continuous monitoring. |
| Insurance Companies | Identity theft, fraud, data breaches, and loss of confidential customer information. | Phishing schemes, data breaches, and identity theft targeting policyholders and employees. | Data encryption, multi-factor authentication, regular security assessments, and robust incident response plans. |
| Payment Processors | Fraudulent transactions, unauthorized access to payment systems, data breaches. | Card skimming, malware infections, phishing attacks, and data theft. | Advanced fraud detection systems, strong encryption protocols, regular security audits, and secure payment gateways. |
Common Data Security Threats for Finance Teams
Finance teams are prime targets for cybercriminals due to the sensitive financial data they handle. Protecting this data is paramount to maintaining trust, preventing financial losses, and upholding regulatory compliance. Understanding the common threats and vulnerabilities is crucial for developing effective security strategies.
Phishing Attacks on Financial Data
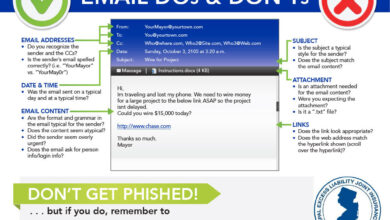
Phishing attacks, where attackers impersonate legitimate entities to trick individuals into revealing sensitive information, pose a significant risk to finance teams. These attacks often target employees through emails, text messages, or malicious websites designed to mimic trusted institutions. Attackers aim to steal login credentials, account information, or financial data. The impact can be devastating, leading to unauthorized access, fraudulent transactions, and reputational damage.
For example, a sophisticated phishing campaign could target executives, gaining access to high-value accounts or initiating wire transfers.
Malware and Ransomware Targeting Financial Systems
Malware and ransomware pose severe threats to financial systems. Malware, including viruses, worms, and Trojans, can infiltrate systems, disrupting operations, stealing data, or causing damage. Ransomware attacks, a more insidious type of malware, encrypt data and demand payment for its release. This can lead to significant downtime, loss of crucial data, and substantial financial losses. For example, a ransomware attack on a bank’s transaction processing system could cripple its operations for days or weeks.
Social Engineering Tactics to Compromise Financial Data
Social engineering tactics exploit human vulnerabilities to gain access to financial data. Attackers leverage psychological manipulation to trick employees into divulging confidential information or granting unauthorized access. This can involve impersonating colleagues, superiors, or even customers to pressure employees into making hasty decisions. For example, an attacker might pose as a senior executive requesting urgent transfer of funds.
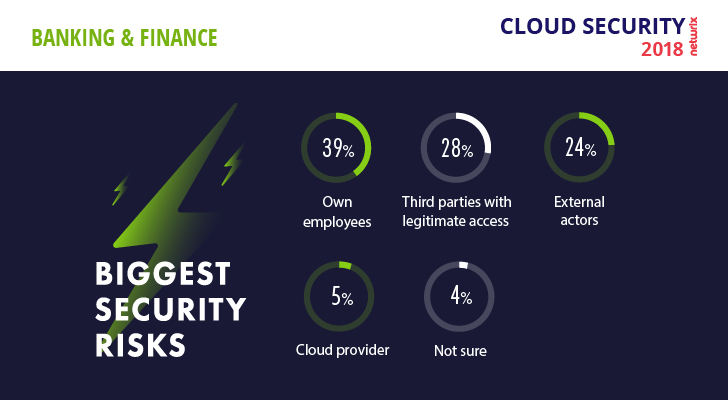
Insider Threats and Malicious Actors
Insider threats, posed by employees with malicious intent or negligence, represent a critical risk. These threats can include unauthorized data access, disclosure, or modification. Similarly, malicious actors, often external to the organization, exploit vulnerabilities to steal financial data. The impact of insider threats can be devastating, ranging from minor data breaches to catastrophic financial losses. A disgruntled employee with access to sensitive accounts could cause extensive damage.
Comparison of Data Breaches in the Finance Sector
| Data Breach | Cause | Impact | Countermeasures |
|---|---|---|---|
| 2021 Bank XYZ Breach | Phishing attack targeting customer accounts | Loss of customer data, reputational damage, financial losses | Enhanced security awareness training, multi-factor authentication, email filtering |
| 2022 Credit Union X Data Breach | Malware infection via compromised email | Unauthorized access to customer accounts, financial losses, regulatory fines | Stronger endpoint security, robust firewall implementation, data encryption |
| 2023 Investment Firm Y Ransomware Attack | Ransomware targeting critical financial systems | Data encryption, significant operational disruption, substantial financial losses | Regular data backups, robust incident response plan, threat intelligence monitoring |
| 2024 Brokerage Firm Z Insider Threat | Employee with access to sensitive accounts steals data | Significant financial losses, reputational damage, legal repercussions | Access controls, background checks, employee monitoring, strict data handling procedures |
This table illustrates the varied causes and consequences of data breaches in the finance sector. The countermeasures highlighted are essential for mitigating future risks. A comprehensive approach to data security is critical for preventing such incidents.
Enhance your insight with the methods and methods of how to clearly communicate feedback and expectations.
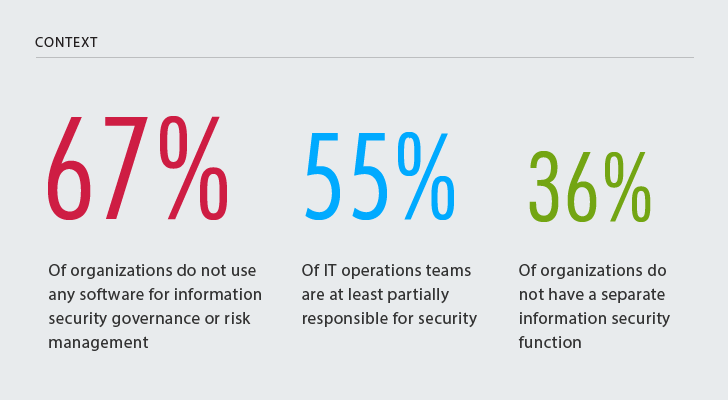
Data Security Vulnerabilities in Financial Systems
Financial institutions are prime targets for cyberattacks, and vulnerabilities within their systems can lead to devastating consequences, including financial losses, reputational damage, and regulatory penalties. Understanding these vulnerabilities is crucial for mitigating risks and safeguarding sensitive financial data. This section delves into the weaknesses in existing financial systems, examining the impact of legacy systems, cloud-based applications, third-party integrations, and inadequate access controls.Legacy systems often lack the modern security features present in newer platforms.
Their outdated architectures and coding practices can create significant vulnerabilities that are difficult to patch or update effectively. This, combined with a lack of resources for comprehensive security audits, leaves them vulnerable to exploits. This inherent weakness poses a considerable risk in the financial sector.
Weaknesses in Existing Financial Systems
Legacy systems, developed decades ago, frequently lack robust security protocols. These systems often rely on outdated encryption methods and lack the security features found in modern applications. The sheer complexity of these systems and the lack of documentation further compound the difficulty in identifying and mitigating vulnerabilities. This legacy infrastructure can represent a significant security risk. The financial implications of breaches can be enormous, causing not only direct financial losses but also reputational damage.
Impact of Legacy Systems on Security Postures
Legacy systems often lack the security features present in newer applications. This can lead to a lack of visibility into potential threats and vulnerabilities. The difficulty in updating and maintaining legacy systems can result in a backlog of security patches, increasing the risk of exploitation. The lack of skilled personnel knowledgeable in these outdated systems further complicates the task of managing security risks.
In some cases, the older technology used in legacy systems may no longer have readily available support or security updates, leaving the organization vulnerable to known exploits.
Vulnerability of Cloud-Based Financial Applications and Data Storage
Cloud-based financial applications and data storage present a unique set of security challenges. While cloud providers often offer robust security measures, vulnerabilities can arise from misconfigurations, inadequate access controls, or insufficient security awareness among users. A common issue is the lack of visibility into the security controls and access privileges of cloud resources, making it difficult to identify and remediate vulnerabilities.
Additionally, the reliance on shared infrastructure and the potential for data breaches from cloud providers or their partners must be carefully considered.
Security Implications of Third-Party Vendors and Integrations
Third-party vendors and integrations can introduce vulnerabilities into financial systems. These vulnerabilities often arise from insufficient vetting of third-party security practices, inadequate security protocols in integrations, and insufficient communication channels between the financial institution and the third-party vendor. Breaches or vulnerabilities in a third-party system can expose sensitive financial data, highlighting the critical need for thorough due diligence and robust security agreements.
Inadequate Access Controls and Unauthorized Data Access
Inadequate access controls are a significant source of vulnerability in financial systems. Insufficient access controls allow unauthorized personnel to access sensitive financial data, leading to breaches and potential financial losses. Insufficient segregation of duties, weak password policies, and insufficient multi-factor authentication procedures can contribute to unauthorized access. Regular security audits and access control reviews are essential to ensure compliance with regulatory standards and reduce the risk of data breaches.
Specific Vulnerabilities and Mitigation Strategies
| Vulnerability | Description | Mitigation Strategy | Example |
|---|---|---|---|
| Weak Passwords | Using easily guessed or predictable passwords. | Implement strong password policies, enforce password complexity requirements, and encourage the use of password managers. | Using “password123” |
| Insecure APIs | APIs that lack proper authentication and authorization mechanisms. | Implement robust API security best practices, including authentication, authorization, and input validation. | APIs that accept user inputs without proper validation. |
| Unpatched Software | Using outdated or unpatched software. | Establish a patch management process, implement automated updates, and prioritize security updates. | Not applying security patches on operating systems or applications. |
| Social Engineering | Manipulating employees into revealing sensitive information. | Implement security awareness training programs, establish clear communication channels, and encourage employees to report suspicious activities. | Phishing attacks targeting employees. |
Protecting Sensitive Financial Data
Safeguarding financial data is paramount for any financial institution. Robust security measures are crucial to prevent unauthorized access, breaches, and financial losses. Implementing strong encryption, multi-factor authentication, and regular security audits is essential for protecting sensitive financial information and maintaining customer trust. Failure to prioritize these measures can lead to significant reputational damage and substantial financial penalties.Protecting financial data involves a multi-layered approach.
It requires a proactive stance, encompassing not just technical safeguards, but also a culture of security awareness within the organization. This extends to the entire finance team, from analysts to executives, ensuring everyone understands their role in maintaining data integrity.
Robust Data Encryption Techniques
Data encryption transforms readable data into an unreadable format, making it unintelligible to unauthorized individuals. Modern encryption techniques utilize strong algorithms and keys to ensure data confidentiality. Advanced encryption standards (AES) are widely used for their high security and efficiency. Employing strong encryption is crucial, especially for sensitive data like account numbers, transaction details, and customer information.
This process is critical in preventing unauthorized access and data breaches, especially in environments with high-value transactions.
Multi-Factor Authentication Methods
Multi-factor authentication (MFA) adds an extra layer of security beyond a simple username and password. It requires users to provide multiple verification methods before accessing sensitive data. This can include something the user knows (password), something the user has (security token), or something the user is (biometric data). MFA significantly reduces the risk of unauthorized access by demanding multiple forms of verification.
For instance, a bank might require a one-time code sent to a registered mobile phone in addition to a password.
Regular Security Audits and Penetration Testing
Regular security audits and penetration testing are vital for identifying vulnerabilities in financial systems. Audits evaluate the effectiveness of existing security controls, while penetration testing simulates real-world attacks to assess the system’s resilience. These evaluations are crucial for proactively addressing potential weaknesses and enhancing security posture. For example, a regular audit might uncover weak access controls, while a penetration test might demonstrate the potential for a phishing attack.
These proactive measures minimize risks and safeguard financial assets.
Incident Response and Data Breach Management Procedures
Having a well-defined incident response plan is critical in case of a data breach. This plan should Artikel procedures for detecting, containing, responding to, and recovering from incidents. It’s crucial to have a clear communication strategy, outlining who is responsible for what during a crisis. This involves rapid containment to limit the damage, notification of affected parties, and investigation into the cause of the breach.
Data Security Awareness Training for Finance Teams, Data security risks for finance teams
Training finance teams on data security best practices is essential. This training should cover topics like recognizing phishing attempts, safe password practices, and the importance of reporting suspicious activities. This training helps create a security-conscious culture within the team, minimizing the risk of human error. For example, training should cover common social engineering tactics and the importance of verifying the legitimacy of emails or requests before providing sensitive information.
Encryption Method Comparison
| Encryption Method | Strengths | Weaknesses | Use Cases |
|---|---|---|---|
| AES (Advanced Encryption Standard) | High security, widely adopted, efficient | Can be computationally intensive for certain applications | General-purpose encryption, including financial data |
| RSA (Rivest-Shamir-Adleman) | Suitable for key exchange, widely used in digital signatures | Can be slower than AES, susceptible to certain attacks if not implemented correctly | Digital signatures, public-key infrastructure |
| Triple DES (3DES) | Backward compatibility with older systems | Less secure than modern alternatives | Legacy systems requiring compatibility with older encryption methods |
| Blowfish | Faster than AES in some implementations | Not as widely adopted as AES, potential vulnerabilities | Specific applications needing speed |
Regulatory Compliance and Data Security

Staying compliant with data security regulations is paramount for financial institutions. Non-compliance can lead to significant financial penalties, reputational damage, and legal repercussions. This section delves into the critical importance of adhering to regulations like GDPR and CCPA, outlining the penalties for non-compliance, and detailing the requirements for data breach notification procedures. Understanding the regulatory landscape and implementing effective compliance strategies is vital for safeguarding sensitive financial data and maintaining trust with customers.
Importance of Adhering to Data Security Regulations
Data security regulations, like GDPR and CCPA, are crucial for protecting individuals’ personal data. These regulations establish strict standards for how organizations collect, use, and store personal information. Adherence demonstrates a commitment to protecting customer privacy and builds trust. Failing to comply can result in severe consequences, including hefty fines and reputational damage.
Penalties for Non-Compliance with Data Security Regulations in Finance
Non-compliance with data security regulations carries significant financial penalties for financial institutions. Fines can range from thousands to millions of dollars, depending on the severity of the violation, the jurisdiction, and the number of affected individuals. For example, under GDPR, organizations can face substantial fines for failing to comply with data breach notification procedures or for inadequately protecting personal data.
These penalties serve as a strong deterrent and emphasize the critical importance of proactive data security measures.
Data Breach Notification Procedures
Data breach notification procedures are critical components of regulatory compliance. These procedures Artikel the steps organizations must take to notify affected individuals and regulatory authorities in the event of a data breach. Prompt and accurate notifications are vital to mitigating the impact of a breach and demonstrating a commitment to transparency and accountability. Failure to adhere to these procedures can lead to further penalties and legal action.
Organizations must establish clear protocols for identifying, assessing, and responding to data breaches.
You also can understand valuable knowledge by exploring cima ethics confidentiality rules.
Overview of Regulatory Frameworks Related to Data Security
Numerous regulatory frameworks govern data security, encompassing various aspects of data handling. These regulations often overlap, creating a complex but necessary landscape for organizations to navigate. The General Data Protection Regulation (GDPR) in Europe and the California Consumer Privacy Act (CCPA) in the US are prominent examples, but other regions and jurisdictions also have their own data protection laws.
Understanding the specific requirements of each applicable regulation is crucial for effective compliance.
Successful Data Security Compliance Strategies in Finance
Financial institutions have implemented various successful strategies for data security compliance. These strategies often involve a multi-faceted approach, combining robust technical safeguards with comprehensive training programs for employees. Regular security assessments, penetration testing, and incident response planning are also essential components. Organizations prioritize establishing clear data governance policies, and implementing a culture of data security awareness among all staff.
Check what professionals state about global cfo survey rebuild revenue streams and its benefits for the industry.
This proactive approach helps to prevent breaches and minimize the impact of any incidents that do occur.
Summary of Key Regulations and Compliance Requirements
| Regulation | Jurisdiction | Key Compliance Requirements | Examples of Penalties |
|---|---|---|---|
| GDPR | European Union | Data minimization, purpose limitation, data subject rights, data breach notification, and security of processing | Millions of Euros |
| CCPA | California, USA | Right to know, right to delete, right to opt-out, and data breach notification | Hundreds of thousands of Dollars |
| HIPAA | USA | Protection of Protected Health Information (PHI) | Significant financial penalties |
| PCI DSS | Worldwide | Protection of cardholder data | Varying, often substantial |
Building a Strong Data Security Culture: Data Security Risks For Finance Teams
A robust data security posture in finance isn’t just about technology; it’s fundamentally about people. A proactive data security culture within a finance team fosters vigilance and responsibility, reducing the likelihood of breaches and ensuring compliance. This proactive approach goes beyond simply enforcing rules; it instills a mindset of security awareness, making every team member a guardian of sensitive financial data.A strong data security culture is not a destination, but a continuous journey of improvement and adaptation.
It’s about integrating security into the daily routines and decision-making processes of the entire team, from junior analysts to senior executives. This requires consistent reinforcement, regular training, and clear communication to ensure everyone understands their role in protecting the organization’s valuable assets.
Importance of Proactive Data Security Culture
A proactive data security culture in finance is crucial for mitigating risks. It’s more than just reacting to threats; it’s about anticipating them and proactively implementing preventative measures. A culture of vigilance ensures that potential vulnerabilities are identified and addressed before they can be exploited. This proactive stance significantly reduces the organization’s exposure to financial losses and reputational damage.
Fostering Security Awareness and Vigilance
Creating a culture of security awareness involves consistent communication and training. Regular security awareness campaigns, using various channels like email newsletters, in-house presentations, and interactive workshops, can effectively disseminate crucial information. The campaigns should focus on real-world scenarios and emphasize the consequences of neglecting security protocols. For example, a campaign demonstrating the impact of phishing attempts can highlight the importance of verifying email links and attachments.
Role of Leadership in Promoting Data Security Best Practices
Leadership plays a pivotal role in establishing and maintaining a strong data security culture. Senior management must actively demonstrate commitment to data security by integrating security considerations into all decision-making processes. This includes allocating resources for training, establishing clear security policies, and holding team members accountable for adhering to those policies. Visible support from leadership is crucial in driving the desired security culture throughout the organization.
Successful Data Security Awareness Campaigns
Several organizations have successfully implemented data security awareness campaigns. One effective strategy is to simulate phishing attacks to test employee awareness and identify vulnerabilities in the security protocols. Regular, interactive quizzes and games can also engage employees and reinforce key security concepts. These campaigns should not only highlight risks but also celebrate successes in maintaining a secure environment.
For example, recognizing and rewarding employees who identify potential security threats.
Implementation of a Comprehensive Data Security Training Program
A comprehensive data security training program is essential for equipping employees with the knowledge and skills to protect sensitive data. The program should cover various aspects, including identifying phishing attempts, recognizing malicious software, and adhering to data handling procedures. The program should be tailored to different roles and responsibilities within the finance team. Training should be regularly updated to reflect the latest threats and best practices.
Key Components of a Robust Data Security Culture
| Role | Responsibilities | Training Requirements | Accountability |
|---|---|---|---|
| All Employees | Adhering to security policies, reporting suspicious activity, practicing safe password management, being cautious of phishing attempts. | Regular security awareness training, phishing simulations, and workshops on data handling procedures. | Hold employees accountable for adhering to the policies and procedures. |
| IT Department | Maintaining and updating security systems, implementing security patches, and providing technical support. | Specialized training on security systems, vulnerability assessments, and incident response protocols. | Responsible for the overall security infrastructure and responding to security incidents. |
| Management | Establishing clear security policies, allocating resources for security initiatives, and promoting a security-conscious culture. | Executive briefings, training on security risks and compliance regulations. | Setting the tone for security within the organization, monitoring progress and providing necessary resources. |
| Security Officers | Developing and implementing security policies, conducting security audits, and investigating security incidents. | Advanced training in security management, threat intelligence, incident response, and compliance regulations. | Responsible for the organization’s security posture and ensuring compliance. |
Emerging Trends in Financial Data Security
The financial sector is constantly evolving, adopting new technologies and facing new challenges. This necessitates a continuous adaptation of security measures to protect sensitive financial data from emerging threats. Staying ahead of the curve requires understanding the impact of these advancements on data security.The rapid integration of artificial intelligence, machine learning, and blockchain technology into financial processes creates both opportunities and risks.
Financial institutions must proactively address these evolving threats and vulnerabilities to maintain trust and protect their customers’ assets.
Artificial Intelligence and Machine Learning in Finance
AI and machine learning (ML) are transforming financial operations, from fraud detection to risk assessment. However, these powerful technologies also introduce new vulnerabilities. AI models can be susceptible to adversarial attacks, where malicious actors manipulate input data to produce inaccurate or misleading results. This could lead to fraudulent transactions being overlooked or legitimate transactions being flagged as suspicious.Moreover, the training data used to develop these models can reflect existing biases, potentially perpetuating unfair or discriminatory outcomes.
Ensuring the fairness, transparency, and robustness of AI/ML systems is crucial for maintaining data security and ethical considerations. Robust testing and validation procedures are essential to mitigate the risks. Financial institutions need to develop robust security protocols and conduct thorough security audits to detect potential vulnerabilities and mitigate risks related to AI and ML implementation.
Blockchain Technology and Data Security
Blockchain technology, known for its decentralized and transparent nature, offers promising solutions for enhancing financial data security. Its immutability and cryptographic hashing ensure data integrity and prevent tampering. However, blockchain itself isn’t inherently secure. The security of blockchain-based systems depends heavily on the underlying cryptographic protocols and the security of the network nodes. A critical issue is the potential for smart contract vulnerabilities, which could expose sensitive financial data if not carefully implemented and audited.Examples of how blockchain is being used include secure tokenization of sensitive data, creating tamper-proof audit trails, and facilitating secure transactions.
However, financial institutions must carefully assess the security implications and potential vulnerabilities before integrating blockchain technology into their systems.
Emerging Technologies and Data Security
Financial institutions are embracing a range of emerging technologies to bolster data protection. These technologies include cloud computing, quantum computing, and Internet of Things (IoT) devices. Each technology brings unique security considerations. Cloud computing, for instance, requires robust access controls and encryption to prevent unauthorized data access. Quantum computing presents a future threat to current encryption methods, demanding the development of post-quantum cryptography.The increased reliance on IoT devices introduces new avenues for attack, requiring strong authentication and data encryption protocols.
Institutions need to develop comprehensive security strategies that encompass all these evolving technologies and their specific vulnerabilities.
Continuous Monitoring and Adaptation
A critical aspect of financial data security is continuous monitoring and adaptation to emerging threats. This involves proactively identifying and responding to new vulnerabilities, as well as adapting security protocols and training programs to reflect the evolving threat landscape. Regular security assessments, penetration testing, and vulnerability scans are essential to maintain a strong security posture.A dynamic approach that anticipates future threats and vulnerabilities is paramount.
This involves staying abreast of emerging technologies and their security implications, and constantly refining security protocols to effectively address potential threats. Developing an adaptable security framework that proactively addresses these emerging technologies is essential.
Comparing Emerging Technologies and Their Impact
| Technology | Potential Benefits | Potential Risks | Mitigation Strategies |
|---|---|---|---|
| Artificial Intelligence/Machine Learning | Enhanced fraud detection, improved risk assessment | Adversarial attacks, bias in data, lack of transparency | Robust model validation, diverse training data, explainable AI |
| Blockchain | Enhanced data integrity, secure transactions | Smart contract vulnerabilities, network security risks | Thorough smart contract audits, secure network protocols |
| Cloud Computing | Scalability, cost-effectiveness | Data breaches, unauthorized access | Strong access controls, data encryption, multi-factor authentication |
| Quantum Computing | Potential for new computational power | Threat to current encryption methods | Development and implementation of post-quantum cryptography |
Wrap-Up
In conclusion, data security risks for finance teams are multifaceted and require a multi-layered approach. This exploration has highlighted the critical need for robust security measures, a strong security culture, and continuous adaptation to emerging threats. By proactively addressing vulnerabilities and staying informed about the latest industry best practices, financial institutions can significantly reduce their risk profile and ensure the safety and integrity of their sensitive data.