Overcoming the G2 Data Access Bottleneck: A Strategic Solution for B2B Competitive Intelligence
G2, standing as a formidable repository of roughly two million verified software reviews spanning tens of thousands of Software-as-a-Service (SaaS) categories, represents one of the internet’s most invaluable public datasets for anyone engaged in competitive intelligence, sales prospecting, or product research within the B2B software ecosystem. Its content, generated by real business users, offers unparalleled insights into product performance, customer satisfaction, and market sentiment. However, as of 2026, the process of extracting this rich data at scale has evolved into an increasingly complex and resource-intensive endeavor, described by many as "comically painful." This article delves into the escalating challenges of accessing G2 data and introduces a sophisticated, cleaner pathway for structured review extraction.
For developers and data scientists who have attempted to programmatically interface with g2.com using standard web scraping libraries such as requests, the narrative is all too familiar and frustratingly consistent. The initial hurdle often presents itself as a Cloudflare Turnstile, a robust CAPTCHA service designed to differentiate human users from bots. Overcoming this only leads to the next formidable barrier: a Kasada challenge, an advanced bot mitigation platform known for its sophisticated behavioral analysis and fingerprinting techniques. Even if one manages to bypass Kasada, subsequent defenses include TLS fingerprint checks, which scrutinize the unique characteristics of the secure connection, followed by intricate behavioral JavaScript puzzles that demand a high degree of browser-like interaction. The gauntlet often concludes with an invisible CAPTCHA, a final layer of verification that operates without overt user interaction. The cumulative effect of these layered defenses means that even meticulously configured headless browsers, fortified with residential proxies to mimic legitimate user traffic, are frequently detected and flagged within processing merely a dozen pages. The G2 review data remains public in principle, yet achieving scalable access has transformed into an arduous cat-and-mouse game, consistently consuming significant engineering hours and disproportionately large proxy budgets. This analysis will explore a more efficient and stable solution: leveraging the zhorex/g2-reviews-scraper Actor on Apify to systematically pull structured reviews, capturing up to 29 distinct data fields, all without the need to manage a single browser instance or rotate a single proxy.
The Indispensable Value of G2 Data in a Data-Driven Economy
Before delving into the mechanics of data extraction, it is crucial to underscore the profound utility of G2 review data. Unlike many other review platforms, G2’s strength lies in its verification process, ensuring that reviews are authored by genuine business users, often providing detailed accounts of their experiences. This verification, combined with the structured and long-form nature of the reviews, renders the data uniquely valuable across several strategic dimensions:
- Competitive Intelligence: Businesses can gain granular insights into competitors’ strengths and weaknesses, identifying features where rivals excel or falter. This extends beyond star ratings to specific comments on usability, support quality, and feature gaps.
- Sales Prospecting and Displacement Plays: By analyzing negative reviews of competing products, sales teams can uncover documented pain points of potential customers, enabling highly targeted outreach and personalized pitches that directly address existing frustrations.
- Product Research and Development: Product managers can identify emerging market needs, validate new feature ideas, and pinpoint areas for improvement in their own offerings by aggregating and analyzing feedback trends across categories.
- Investment Due Diligence: Private equity firms and venture capitalists utilize G2 data to conduct robust due diligence on potential SaaS acquisitions, assessing product-market fit, customer satisfaction trends, and the veracity of growth narratives.
- Customer Success and Churn Prevention: Proactive monitoring of reviews, particularly low-star ratings for one’s own product or competitors, can serve as an early warning system for potential churn risks or opportunities to acquire dissatisfied customers.
In essence, G2 data provides a qualitative and quantitative pulse on the B2B software market, offering actionable intelligence that can inform strategic decisions from product roadmap planning to sales strategy and investment analysis. The sheer depth and breadth of this verified feedback make its acquisition a strategic imperative for many organizations operating in the competitive B2B landscape.
The Escalating Arms Race: A Chronology of Anti-Scraping Defenses
The journey to G2’s current state of robust bot defense is a reflection of a broader industry trend where valuable public data increasingly becomes a target for automated extraction. While specific timelines can be difficult to pinpoint precisely without G2’s internal logs, the evolution of its defenses mirrors general developments in web security:
- Early 2020s: Initial Defenses: G2, like many high-traffic sites, likely began with basic IP-based rate limiting and simple CAPTCHAs. Cloudflare’s widespread adoption in this period introduced an effective initial layer against volumetric attacks and known bot signatures. The Cloudflare Turnstile, a more advanced version, would have been integrated as the sophistication of scraping tools grew.
- Mid-2020s: The Rise of Behavioral Analysis: As scrapers evolved to mimic browser headers and basic user agents, platforms like G2 turned to more advanced solutions. Kasada emerged as a leader in this space, employing machine learning to analyze user behavior, mouse movements, keyboard interactions, and network characteristics to detect non-human activity. This represented a significant leap from static fingerprinting to dynamic, real-time threat detection.
- Late 2020s (leading to 2026): Advanced Fingerprinting and JS Challenges: The current landscape in 2026 sees an amalgamation of these technologies, further enhanced by TLS fingerprinting (analyzing the unique "handshake" of a client’s TLS connection), and complex JavaScript puzzles. These puzzles are designed to be computationally intensive or require specific DOM interactions that are trivial for a human but difficult and resource-intensive for an automated script to execute correctly without full browser emulation. The invisible CAPTCHA layers further refine this by constantly evaluating user legitimacy in the background.
This escalating arms race has transformed web scraping from a relatively straightforward technical task into a specialized cybersecurity challenge. Each new defense mechanism from platforms like G2 necessitates more sophisticated and costly countermeasures from those attempting to extract data, creating an unsustainable cycle for many businesses. The underlying rationale for G2’s investment in these defenses is multi-faceted: to protect their intellectual property, maintain the integrity of their platform, ensure fair access to their data, manage server load, and, significantly, to monetize data access through official channels.
The Impasse: Limitations of Official Channels and the Folly of DIY Scraping
Faced with the imperative to access G2 data, organizations typically encounter two primary, yet deeply flawed, pathways: the official G2 API or a do-it-yourself (DIY) scraping solution.
The Official G2 API: A Gated Community
G2 does indeed offer a paid API, but its accessibility is severely restricted, primarily gated behind an enterprise contract. This entails a lengthy procurement process, often requiring weeks for contract negotiation and provisioning. Furthermore, it typically necessitates a seat license on the G2 side for each user accessing the data. Crucially, the official API is generally limited in scope, restricting users to data pertaining to their own product and, at best, a handful of explicitly named competitors. This fundamental limitation means that the API is not designed for comprehensive market analysis; pulling the full set of reviews for an entire category, such as "CRM Software" or "Marketing Automation," across all vendors within that category, is simply not an option. G2’s business model dictates that broad, unfettered access to competitor data is a premium service, often requiring direct, bespoke data licensing agreements, which are prohibitively expensive and rare.
The DIY Scraping Quagmire: A Costly and Unstable Endeavor
The alternative – developing and maintaining an in-house scraping solution – presents its own set of formidable challenges, often proving to be a false economy. As the anti-scraping technologies have matured, DIY scrapers are almost immediately detected and blocked. The quote from a growth engineer at a mid-market PLG startup succinctly captures this frustration: "We burned six weeks and about $4,000 in proxies before admitting our in-house G2 scraper was never going to be stable." This statement reflects a widespread industry experience.
The costs associated with DIY scraping are multi-layered. Proxy bills for rotating residential IPs, essential for mimicking genuine user traffic and avoiding IP-based blocks, can easily range from $500 to $2,000 per month for even modest volumes of data. Beyond monetary costs, the engineering overhead is substantial. Every time G2 updates its anti-bot measures – introducing a new JavaScript challenge, tweaking a TLS fingerprint check, or updating behavioral detection algorithms – existing Playwright or Selenium scripts inevitably break. This often occurs at inconvenient times, like 3 AM, requiring engineers to divert critical resources away from product development to spend entire Saturdays "fingerprinting headers" or reverse-engineering new JavaScript challenges. The maintenance burden is continuous, unpredictable, and ultimately unsustainable for most teams that lack dedicated cybersecurity or anti-bot expertise.
The Zhorex/G2-Reviews-Scraper Actor: A Strategic Bypass
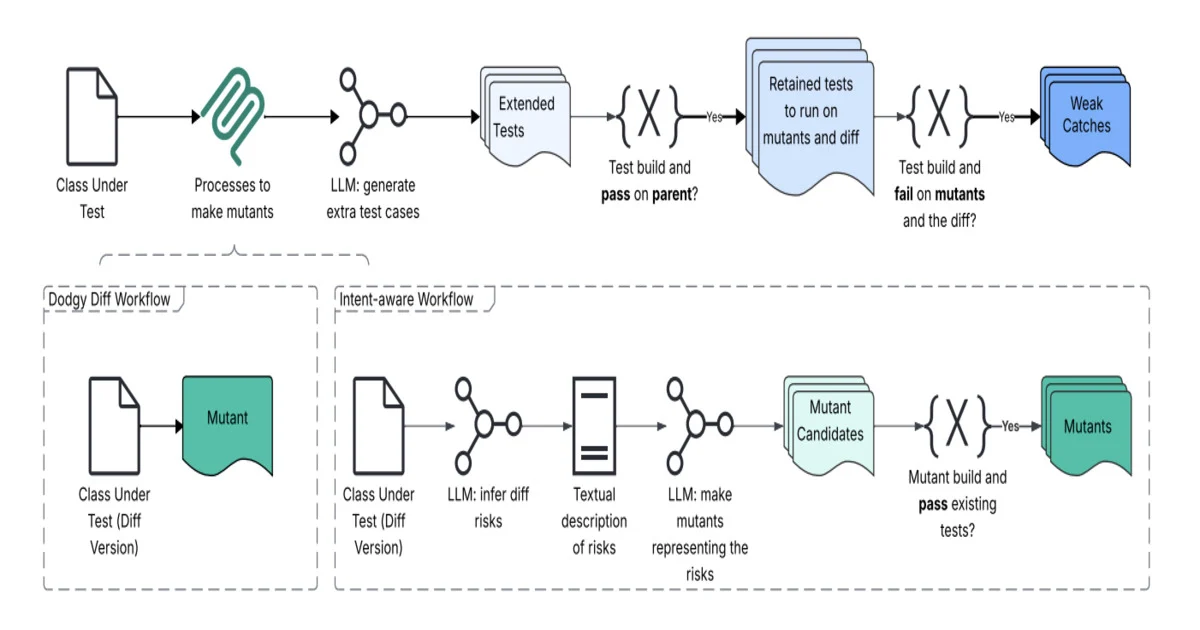
In response to this growing impasse, specialized solutions have emerged that offer a viable alternative. The zhorex/g2-reviews-scraper Actor, hosted on the Apify platform, represents a significant leap forward in reliably accessing G2 data. Its core innovation lies in its ability to bypass the complex layered defenses by directly calling G2’s public review feed. This implies that the Actor has identified and leverages internal API endpoints that G2 uses for its own public-facing display, which are typically less aggressively protected than the main website UI designed for human interaction.
This architectural approach eliminates the need for:
- Browser Emulation: No headless browsers are launched, significantly reducing computational overhead and the complexity of mimicking human browser behavior.
- Proxy Rotation: The Actor does not require users to supply or manage residential proxies, removing a major cost and maintenance headache.
- Kasada Bypass Hacks: The fundamental approach sidesteps the need to actively defeat Kasada or other behavioral analysis systems, leading to superior stability.
The result is a streamlined process where users simply provide a product URL or slug, and the Actor returns rich, structured JSON data. The feature set of this Actor is designed for comprehensive data acquisition:
- Deep Field Extraction: It captures 29 fields of review data, including granular sub-ratings, reviewer demographics, review content (likes, dislikes, recommendations), and publication metadata.
- Flexible Input: Supports specific product URLs or product slugs, allowing for targeted data collection.
- Filtering Capabilities: Users can specify
maxReviewsPerProduct,minRating,maxRating,dateFrom, andlanguageto refine their data requests, ensuring relevance and efficiency. - Inclusion Options: Allows for the inclusion of sub-ratings and reviewer profile information, crucial for deeper analysis.
- Multiple Export Formats: Outputs data in JSON, CSV, XLSX, and JSONL, facilitating easy integration into various analytical workflows and data warehouses.
Comparative Analysis: A Clear Advantage
A direct comparison highlights the strategic and operational advantages of the zhorex/g2-reviews-scraper Actor over the other two prevalent options:
| Capability | G2 Official API | DIY Scraper + Residential Proxies | zhorex/g2-reviews-scraper |
Analytical Implications |
|---|---|---|---|---|
| Access to competitor reviews | No (own product only) | Yes, if you can keep it running | Yes | Critical for competitive intelligence. Official API severely limits market understanding; DIY is unstable; Actor provides consistent, broad market view. |
| Kasada / JS challenge handling | N/A | Your problem, breaks weekly | Handled, no browser needed | Direct impact on stability and maintenance. DIY requires constant, specialized engineering effort; Actor abstracts away complexity, ensuring reliability. |
| Setup time | Weeks (contract + provisioning) | Days to weeks | Minutes | Time-to-insight. Official API is bureaucratic; DIY requires significant development; Actor offers near-instant deployment, enabling rapid data acquisition. |
| Cost at 10k reviews/month | Custom enterprise quote | ~$300-600 proxies + eng time | $50 | Significant ROI. DIY costs escalate quickly with proxies and invaluable engineering time; Actor provides a predictable, low-cost model, making advanced analytics accessible. |
| Sub-ratings included | Yes | Usually not (hard to extract reliably) | Yes (29 fields) | Depth of insight. Sub-ratings are vital for granular product analysis; DIY often struggles with inconsistent extraction; Actor guarantees comprehensive data points. |
| Export formats | JSON via API | Whatever you build | JSON, CSV, XLSX, JSONL | Flexibility and integration. Actor provides diverse formats for seamless integration into BI tools, data warehouses, and analytics platforms, reducing post-extraction processing. |
| Maintenance burden | Low (for limited scope) | High | None | Operational efficiency. DIY is a perpetual drain on engineering resources; Actor provides a "set-it-and-forget-it" solution, freeing up internal teams for analysis rather than maintenance. |
This table clearly demonstrates that for organizations seeking broad, reliable, and cost-effective access to G2 review data for competitive intelligence and market analysis, the zhorex/g2-reviews-scraper Actor offers a superior and more sustainable solution. The implied cost savings, particularly in engineering hours, are substantial, allowing teams to focus on deriving insights rather than battling anti-bot systems.
Real-World Applications: Transforming Data into Strategic Action
The availability of consistently structured G2 data unlocks a multitude of powerful use cases that can significantly impact business strategy and operational efficiency:
1. SaaS Sales Displacement Plays:
Imagine a sales team for a CRM solution. They configure a nightly automated job that pulls all 1- and 2-star reviews for their three primary competitors. Each newly acquired review is then fed into a Large Language Model (LLM) configured to extract the specific complaint or pain point articulated by the reviewer, alongside the reviewer’s company name and industry. The output is a highly prioritized outbound sales list where every lead is accompanied by a documented, explicit pain point, expressed in the prospect’s own words. This hyper-personalization dramatically increases the efficacy of outreach; open rates on personalized sequences built from these real G2 complaints routinely run 2-3 times higher than generic cold outbound campaigns, leading to more qualified leads and faster sales cycles.
2. Category-Level Feature Gap Analysis:
Consider a product manager at a leading marketing automation vendor. Their objective is to understand the competitive landscape and identify potential product roadmap opportunities. They use the Actor to scrape every review within the "Marketing Automation" category filed over the past 12 months, accumulating approximately 40,000 reviews across 30 different products. The "dislikes" sections of these reviews are then processed using advanced natural language processing (NLP) techniques, such as embedding models, to cluster similar complaints. By analyzing the frequency of these clusters per vendor, the product manager can generate a heatmap. This heatmap visually identifies features that are consistent weak spots across the entire category (representing excellent roadmap input for industry-wide innovation) and those that are only weak for specific competitors (providing valuable competitive collateral for sales and marketing teams).
3. Churn and Renewal Risk Signals for Customer Success:
A customer success team at an observability vendor implements a rolling, automated scrape of their own product’s reviews, alongside those of their top five competitors. This system is scheduled to run hourly. Any new 1- or 2-star review that mentions an integration or feature directly covered by their product is immediately routed to a dedicated Slack channel. This acts as a real-time early-warning system for potential account risk, allowing customer success managers to proactively engage with at-risk accounts before they churn. Simultaneously, it generates a real-time queue of "switch-ready" prospects – customers dissatisfied with a competitor’s product who might be receptive to a new solution.
4. Private Equity Due Diligence:
A private equity analyst is evaluating a potential SaaS acquisition. Beyond financial statements and growth projections, they need to reality-check the seller’s narrative about product quality and market position. The analyst utilizes the Actor to scrape five years of G2 review history for the target company and three comparable vendors. They then analyze trends in monthly average star ratings, deltas in specific sub-ratings (e.g., ease of use, quality of support), and review volume growth. This longitudinal data provides an independent, objective assessment of customer sentiment, product evolution, and market perception, becoming a crucial component of the investment memo and informing valuation.
These examples underscore how accessible, structured G2 data, when integrated into analytical workflows, can provide a competitive edge, inform strategic decisions, and drive tangible business outcomes across various departments.
Transparent Pricing and Sustainable Access
The zhorex/g2-reviews-scraper Actor operates on a clear and predictable pricing model: $0.005 per review scraped, billed directly through the Apify platform. Crucially, because the Actor does not rely on browser emulation, the associated platform compute usage is negligible, keeping overall costs low.
Consider these worked examples to illustrate the cost-effectiveness:
- 10,000 reviews: $50
- 100,000 reviews: $500
- 1,000,000 reviews (1 million): $5,000
This pricing stands in stark contrast to the costs associated with a DIY build. For instance, a single month of residential proxies for collecting 100,000 reviews could easily run from $1,500 to $3,000, not including the invaluable engineering time required to develop, maintain, and constantly debug the Kasada bypass logic. For most teams, the break-even point for adopting this Actor over an in-house solution is well under a week, making it an economically compelling choice.
Frequently Asked Questions: Addressing Key Concerns
Is scraping G2 reviews legal?
The legality of scraping publicly accessible data has been repeatedly affirmed in US courts, most notably in the landmark hiQ v. LinkedIn case. The Actor only collects data that any logged-out visitor can see, meaning it operates within the bounds of public data access. However, the onus is on the user to ensure their subsequent use and redistribution of the data comply with relevant laws and ethical guidelines. For instance, republishing full review text as one’s own content is generally discouraged, and strict adherence to GDPR (General Data Protection Regulation) is essential when processing reviewer metadata for individuals within the European Union. Users must exercise due diligence in their data governance.
Do I need proxies or a Kasada solver?
No. The Actor’s design leverages G2’s public review feed directly, bypassing the need to interact with the main website’s bot detection mechanisms. Therefore, users are not required to supply their own proxies, browser fingerprints, or CAPTCHA solver tokens. This significantly simplifies deployment and eliminates a major source of ongoing maintenance.
How fresh is the data?
Reviews are scraped live at the time of the run. If a review was published five minutes before your execution, it will be included in the dataset. For organizations requiring continuous monitoring and the freshest possible data, the Actor can be scheduled to run hourly or daily via Apify Schedules, ensuring an always up-to-date feed.
What is the rate limit?
Practically speaking, users are limited by Apify’s platform concurrency and the Actor’s internal pacing mechanisms, rather than by G2 actively blocking requests. The Actor is designed for efficient, large-scale data collection, typically yielding approximately 500-1,000 reviews per minute per run. Furthermore, runs can be parallelized across multiple product URLs, allowing for even greater throughput when collecting data for numerous products simultaneously.
Can I get all 29 fields or is that a premium tier?
All 29 available fields of review data are included as standard at the flat $0.005 per review rate. There is no feature-gated premium tier for deeper data access, ensuring transparency and equal access to comprehensive information.
How do I export to my warehouse?
Apify provides robust export capabilities. Datasets can be downloaded in various formats including JSON, CSV, XLSX, JSONL, RSS, and as an HTML table. For seamless integration with data warehouses, Apify offers native integrations for popular cloud storage solutions like Amazon S3 and Google Drive, as well as customizable webhooks. A common and highly efficient pattern for large datasets involves exporting data as JSONL files to an S3 bucket, from where it can then be easily ingested using a COPY command into data warehouses such as Snowflake or Google BigQuery.
Holistic B2B Intelligence: Complementing G2 with Capterra and Beyond
For a truly comprehensive competitive intelligence strategy in the B2B software market, relying solely on G2, while highly valuable, might not provide the full picture. G2 tends to skew towards mid-market and enterprise SaaS solutions, reflecting the purchasing power and review contribution patterns of larger organizations. Capterra, owned by Gartner, offers a crucial complement, leaning more towards the small and medium-sized business (SMB) segment and boasting broader coverage of vertical-specific software (e.g., construction, healthcare, legal tech) that might not be as heavily reviewed on G2.
Recognizing this need for holistic coverage, the companion Actor zhorex/capterra-reviews-scraper has been developed, adhering to the same schema philosophy and designed to pair cleanly with the G2 Actor in a single data pipeline. By integrating data from both platforms, businesses can achieve a more nuanced and complete understanding of customer sentiment across different market segments and industry verticals. Furthermore, for organizations tracking sentiment on Chinese-language software or consumer platforms, the zhorex/weibo-scraper provides dedicated coverage for the APAC market, enabling a truly global perspective on product perception and market trends. This layered approach ensures that no critical data source is overlooked in the pursuit of actionable insights.
Embarking on Data-Driven Insights
The era of struggling with complex anti-scraping technologies for G2 data is over. The zhorex/g2-reviews-scraper Actor offers a robust, stable, and cost-effective solution for accessing this critical B2B intelligence. The Actor page, complete with a full input schema and the option for a free trial run, is live and accessible at: https://apify.com/zhorex/g2-reviews-scraper.
By simply dropping in a product URL and initiating a run, users can acquire a clean, structured JSON dataset within minutes, accessible directly from the Apify console. This eliminates the need for expensive proxy contracts, the perpetual cat-and-mouse game with Kasada and other anti-bot measures, and the dreaded 3 AM maintenance calls, allowing businesses to finally focus their valuable resources on analysis and strategic decision-making rather than data acquisition battles.