CIMA Ethics Confidential Information A Deep Dive
CIMA ethics confidential information is paramount in today’s business world. This in-depth exploration delves into the core principles of the Chartered Institute of Management Accountants (CIMA), focusing specifically on handling confidential information. We’ll examine the importance of confidentiality in various professional contexts, from accounting to finance, and explore practical scenarios where CIMA members might encounter sensitive data.
From defining the specific aspects of CIMA ethics related to confidential information, to outlining different types of confidential data, we’ll explore common pitfalls and the crucial procedures for safeguarding this sensitive data. We’ll analyze potential ethical dilemmas, the decision-making process, and the importance of professional judgment. Furthermore, we’ll discuss various security measures, best practices, and the consequences of breaching confidentiality, providing real-world case studies to illustrate the points.
Defining CIMA Ethics and Confidential Information
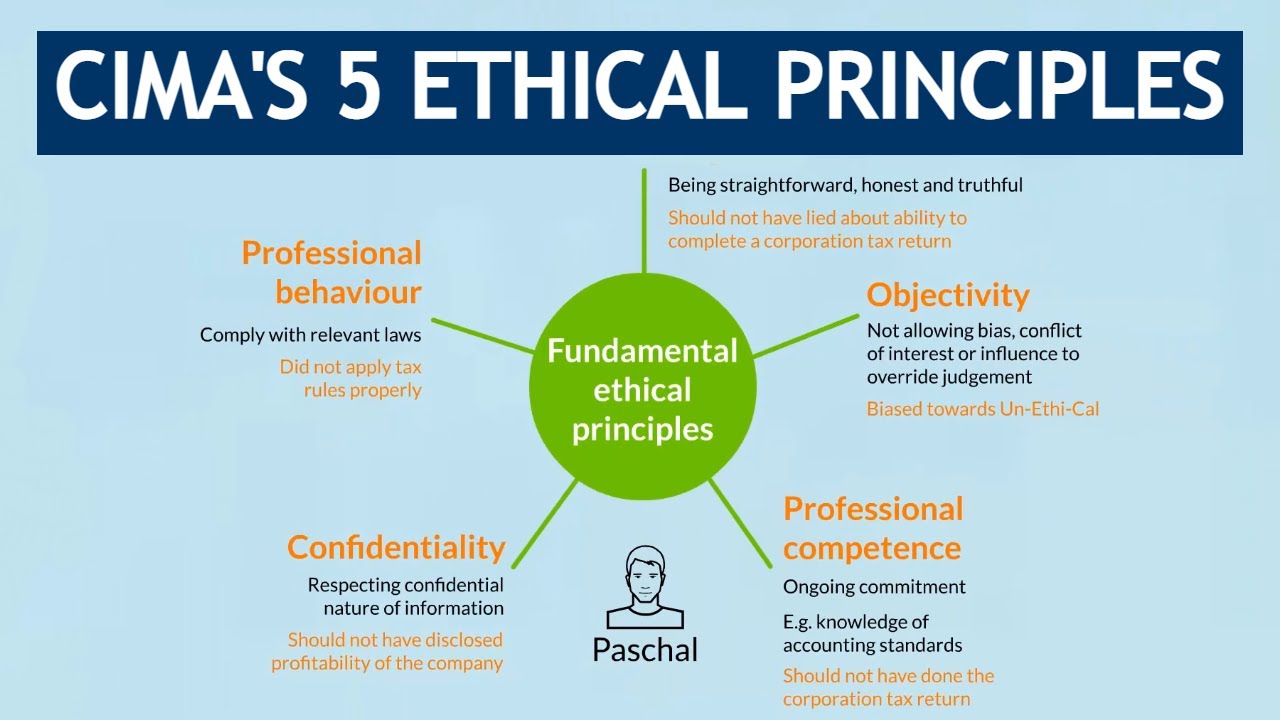
Navigating the complex world of accounting and finance requires a strong ethical compass. CIMA (Chartered Institute of Management Accountants) sets a high standard for its members, emphasizing integrity and professional conduct. Understanding CIMA ethics, particularly regarding confidential information, is crucial for maintaining trust and upholding the highest standards of professionalism.CIMA’s ethical principles underpin the conduct of its members.
These principles guide decision-making and actions in all professional contexts, including the handling of confidential information. Adherence to these principles is essential for building a reputation of trust and credibility within the business community.
Obtain direct knowledge about the efficiency of positive outlook financial services work in europe through case studies.
CIMA Ethical Principles
CIMA’s ethical principles are a cornerstone of professional conduct for its members. These principles provide a framework for making ethical decisions in various situations, particularly when dealing with sensitive or confidential information. These principles aim to ensure honesty, fairness, objectivity, and responsibility in all professional dealings.
Obtain recommendations related to global cfo survey rebuild revenue streams that can assist you today.
Confidential Information in CIMA Ethics
Confidentiality is a vital aspect of CIMA ethics. It encompasses the duty to safeguard sensitive information obtained in the course of professional work. This includes protecting information from unauthorized disclosure, use, or dissemination. The importance of maintaining confidentiality extends beyond legal obligations; it’s crucial for maintaining trust and credibility in business relationships.
Importance of Confidentiality
Confidentiality is paramount in business and professional settings. It fosters trust among stakeholders, including clients, colleagues, and the wider business community. Maintaining confidentiality ensures the security of sensitive information, preventing potential harm and damage to reputation.
Examples of Confidentiality in Accounting and Finance
Numerous situations in accounting and finance necessitate strict confidentiality. For example, client financial data, internal financial projections, and strategic business plans often contain highly sensitive information requiring strict confidentiality. Sharing this information without authorization can lead to significant financial losses, reputational damage, and legal repercussions. A financial advisor sharing a client’s investment strategy with a competitor is a clear violation of confidentiality.
Types of Confidential Information Relevant to CIMA Professionals
Understanding the various types of confidential information is crucial for CIMA professionals. This knowledge helps them to categorize and protect different types of data appropriately.
| Category | Description | Examples |
|---|---|---|
| Client Data | Financial records, personal information, and sensitive business details of clients. | Client budgets, transaction history, and financial projections. |
| Company Data | Internal financial statements, business plans, and strategic initiatives. | Internal reports, research documents, and development strategies. |
| Market Research | Confidential data gathered during market research, competitive analysis, and industry trends. | Customer feedback, competitor pricing data, and market share insights. |
| Employee Data | Salary information, personal details, and performance reviews of employees. | Payroll records, personnel files, and performance appraisals. |
| Legal Documents | Agreements, contracts, and other legally binding documents. | Contracts, non-disclosure agreements, and legal correspondence. |
Confidentiality in Practice: Cima Ethics Confidential Information
Protecting confidential information is paramount for CIMA members. It’s not just about avoiding legal trouble; it’s about upholding professional integrity and building trust with clients, colleagues, and the wider business community. This section delves into practical applications of confidentiality, exploring common scenarios, potential breaches, and the procedures for maintaining data security.Confidentiality in the professional world goes beyond simply keeping secrets.
It’s a crucial component of ethical conduct and responsible business practices. It requires a proactive approach to safeguarding information, understanding its implications, and recognizing the potential harm from breaches.
In this topic, you find that how to clearly communicate feedback and expectations is very useful.
Common Scenarios Involving Confidential Information
CIMA members frequently encounter confidential information in various professional contexts. Client data, financial projections, strategic plans, and internal memos all fall under this category. Examples include:
- Negotiating contracts: Confidential information is often shared during contract negotiations to protect the interests of the parties involved.
- Preparing financial reports: Financial projections, budgets, and other sensitive financial data must be treated with strict confidentiality.
- Participating in client meetings: Discussions during meetings, including details about strategies, client needs, and competitive analysis, should be kept confidential.
- Handling sensitive employee information: Payroll details, performance reviews, and other personal data require strict confidentiality.
Breaches of Confidentiality and Consequences
Breaches of confidentiality can have severe consequences, impacting both individuals and organizations. Examples include:
- Sharing sensitive client data with unauthorized parties: This could lead to reputational damage, legal action, and financial penalties.
- Unauthorized access to and disclosure of financial projections: Such actions can result in significant financial losses and damage to the organization’s credibility.
- Revealing confidential strategic plans to competitors: This can severely undermine a company’s competitive advantage.
- Misuse of internal memos: Unauthorized disclosure of confidential information can result in internal conflict and potentially harm the reputation of the company or the involved parties.
Legal and Regulatory Frameworks
Several legal and regulatory frameworks govern the handling of confidential information. These include data protection laws, such as GDPR (General Data Protection Regulation) in Europe, and various national and international laws concerning trade secrets and intellectual property. Specific industry regulations may also apply.
“Data protection laws require organizations to implement measures to protect personal data and prevent unauthorized access or disclosure.”
Procedures for Handling Confidential Information
Robust procedures for handling confidential information are crucial. These include:
- Implementing access controls: Restricting access to sensitive information to authorized personnel only.
- Using encryption: Protecting data through encryption techniques to prevent unauthorized access.
- Developing clear policies and guidelines: Establishing comprehensive policies and guidelines on the handling of confidential information.
- Training employees: Providing regular training to all personnel on confidentiality protocols.
Comparing Approaches Across Industries
Different industries adopt varying approaches to safeguarding confidential information. The healthcare industry, for example, has stringent regulations regarding patient data, while the financial sector emphasizes strict adherence to banking regulations. The tech industry often focuses on sophisticated data security measures to protect intellectual property.
Responsibilities of CIMA Members Regarding Confidential Information
| Responsibility | Description |
|---|---|
| Confidentiality | Maintaining the confidentiality of all information entrusted to the member. |
| Integrity | Acting honestly and transparently in all professional dealings. |
| Objectivity | Making impartial judgments based on relevant evidence and avoiding bias. |
| Professional competence and due care | Applying the required knowledge and skills diligently to handle confidential information appropriately. |
| Professional behaviour | Conducting oneself with integrity and respect in all professional interactions. |
Ethical Dilemmas and Confidential Information
Navigating the complexities of accounting and finance often involves handling sensitive information. Maintaining confidentiality is paramount, but situations can arise where ethical dilemmas emerge, testing the commitment of professionals to upholding the highest standards. CIMA members face unique pressures in these situations, demanding a robust framework for ethical decision-making. This exploration delves into the potential ethical pitfalls surrounding confidential information and how CIMA members can navigate them effectively.Confidentiality in accounting and finance is not merely a best practice; it’s a fundamental aspect of trust and professional responsibility.
Breaching confidentiality can have severe consequences, ranging from reputational damage and legal repercussions to significant financial losses for clients and organizations. A clear understanding of the ethical dilemmas and a structured approach to resolving them are crucial for upholding integrity and maintaining the credibility of the profession.
Potential Ethical Dilemmas Related to Confidential Information
Understanding the potential conflicts is vital for anticipating and addressing them proactively. These conflicts often arise when professional duties clash with personal interests or when external pressures jeopardize the confidentiality of sensitive information. Examples include situations where:
- A member discovers a potential fraud within their organization but is hesitant to report it due to fear of retribution or the potential for damaging the firm’s reputation.
- A member receives confidential information during a professional engagement and feels tempted to use it for personal gain, such as making investments based on this knowledge.
- A member is faced with a conflict of interest due to dual relationships with multiple clients, each requiring confidentiality that may clash.
Decision-Making Process for CIMA Members
CIMA members are expected to apply a structured decision-making process when confronting ethical conflicts. This process involves several crucial steps:
- Identifying the ethical issue: Carefully analyze the situation to pinpoint the specific ethical concern. This involves recognizing the conflicting values and interests involved. This step is crucial to determine the scope of the issue and the potential ramifications.
- Gathering all relevant information: Collect all available data and evidence to thoroughly understand the context of the dilemma. Consider the perspectives of all stakeholders involved.
- Considering the CIMA Code of Ethics: Apply the principles Artikeld in the CIMA Code of Ethics to evaluate the actions. Referencing the code ensures that decisions align with the expected standards of conduct.
- Seeking advice and guidance: Consulting with senior colleagues, mentors, or ethics committees within CIMA can provide valuable perspectives and ensure the decision is robust and defensible.
- Evaluating possible actions: Weigh the potential consequences of each course of action, taking into account the impact on all stakeholders and the organization. Consider the possible long-term implications.
- Implementing the chosen action: Act decisively and transparently, while ensuring that the chosen action aligns with the CIMA Code of Ethics.
Role of Professional Judgment in Handling Confidential Information
Professional judgment plays a crucial role in navigating ethical dilemmas involving confidential information. It’s not a simple application of rules but a nuanced evaluation of the specific situation and the implications of various actions. It involves considering the specific facts, the potential impact on stakeholders, and the broader context.
Importance of Seeking Guidance and Advice
When faced with ethical dilemmas, seeking guidance and advice is not a sign of weakness but a demonstration of professional responsibility. Consulting with experienced colleagues, mentors, or the CIMA ethics committee can offer invaluable insights and ensure the decision aligns with the highest ethical standards.
Ethical Frameworks Applicable to Confidential Information Issues
Different ethical frameworks can be used to assess the ethical implications of confidential information. A framework should guide the decision-making process by providing a structured approach for considering the various factors.
| Ethical Framework | Description |
|---|---|
| Deontological Ethics | Focuses on moral duties and rules. Actions are judged based on adherence to established principles, such as the duty to keep confidential information. |
| Teleological Ethics | Considers the consequences of actions. The best course of action is the one that maximizes overall well-being and minimizes harm to stakeholders. |
| Virtue Ethics | Emphasizes the character and integrity of the individual. A virtuous professional would prioritize confidentiality as a core value. |
Protecting Confidential Information
Safeguarding confidential information is paramount in today’s interconnected world. This crucial aspect of ethical conduct extends beyond simple discretion; it necessitates proactive measures to prevent unauthorized access and disclosure. Effective protection requires a multifaceted approach encompassing robust security measures, well-defined policies, and a commitment from all stakeholders.
Security Measures for Confidential Information
Protecting confidential data involves a range of security measures. These are not just theoretical concepts but practical tools that, when implemented correctly, can significantly reduce the risk of breaches. This proactive approach ensures compliance with regulations and maintains the integrity of sensitive information.
- Access Controls: Implementing strict access controls is essential. These controls dictate who can access specific data, and under what circumstances. This can be achieved through various methods, including user authentication (passwords, multi-factor authentication), authorization levels (read-only, edit, administrator), and time-based restrictions. Strong passwords, unique to each user, are a crucial first step in protecting sensitive information.
- Data Encryption: Encrypting sensitive data is a critical step in protecting it. Encryption transforms readable data into an unreadable format, making it inaccessible to unauthorized individuals. This is particularly vital for data stored electronically or transmitted across networks. Encryption algorithms like AES-256 provide robust protection against unauthorized decryption. Examples include using encryption for email communications, databases, and cloud storage.
- Physical Security: Protecting physical documents containing confidential information is equally important. Restricting access to physical locations where confidential documents are stored, using locked cabinets, and employing secure disposal methods are all crucial elements of physical security.
- Network Security: Protecting the network infrastructure that stores and transmits confidential information is a vital component of comprehensive data security. Firewalls, intrusion detection systems, and regular security audits help prevent unauthorized access and malicious activities. This includes measures to protect against phishing scams, malware, and denial-of-service attacks.
Implementing Data Protection Policies and Procedures
Effective data protection hinges on well-defined policies and procedures. These policies Artikel the responsibilities of individuals and departments in handling confidential information. They provide a framework for consistent and reliable protection.
- Policy Development: Develop a comprehensive data protection policy that clearly defines acceptable use, access controls, and procedures for handling confidential information. This policy should address data classification, storage, transmission, and disposal. The policy should be reviewed and updated regularly to reflect evolving threats and best practices.
- Procedure Implementation: Implement procedures that translate the policy into actionable steps. Procedures should Artikel specific actions to be taken when handling confidential information, including procedures for reporting suspected breaches and for managing access requests. This ensures consistency in handling sensitive information across the organization.
- Training and Awareness: Regular training and awareness programs are essential to ensure employees understand and adhere to data protection policies and procedures. Training should cover the importance of confidentiality, the risks of unauthorized disclosure, and the appropriate response to suspicious activities.
Data Encryption and Access Controls
Data encryption and access controls are fundamental to protecting confidential information. These measures act as a layered defense against unauthorized access and use.
Data encryption transforms readable data into an unreadable format, safeguarding it from unauthorized access.
Strong access controls limit access to authorized personnel, thereby reducing the potential for misuse. Implementing multi-factor authentication, role-based access control, and regular security audits are key components of effective access control.
Secure Communication Methods
Secure communication channels are essential for transmitting confidential information. These channels should employ encryption and other security measures to protect the integrity and confidentiality of the data being transmitted.
- Virtual Private Networks (VPNs): VPNs create secure encrypted connections over public networks, protecting data transmitted between users and the organization’s network.
- Secure Messaging Platforms: Dedicated secure messaging platforms offer encrypted communication channels, ensuring that messages are only accessible to authorized recipients.
- Secure Email: Encrypting emails using secure protocols like TLS/SSL can protect sensitive data transmitted via email. This helps prevent unauthorized interception of confidential information.
Best Practices for Maintaining Confidentiality
Maintaining the confidentiality of sensitive data requires a commitment to best practices across all aspects of data handling. A structured approach ensures consistent protection.
| Best Practice | Description |
|---|---|
| Data Classification | Categorize data based on sensitivity level to determine appropriate security measures. |
| Access Control | Implement strict access controls to limit access to authorized personnel. |
| Regular Security Audits | Conduct regular security audits to identify vulnerabilities and address any weaknesses. |
| Incident Response Plan | Develop a comprehensive incident response plan to address data breaches and other security incidents. |
| Employee Training | Provide regular training to employees on data protection policies and procedures. |
Consequences of Breaching Confidentiality
Protecting confidential information is crucial in all professional settings. A breach of confidentiality can have severe repercussions for individuals, organizations, and stakeholders, ranging from financial penalties to reputational damage. Understanding these consequences is essential for anyone handling sensitive data.
Potential Penalties for Breaching Confidentiality
Breaching confidentiality can lead to a variety of penalties, both legal and professional. These penalties can vary depending on the nature of the breach, the severity of the harm caused, and the specific regulations in place. Financial penalties, such as fines or compensation for damages, are common outcomes. Moreover, individuals responsible for breaches may face disciplinary action, including warnings, suspension, or even termination of employment.
Legal action can also result in significant penalties, such as lawsuits and criminal charges in serious cases.
Impact on Individuals, Organizations, and Stakeholders
A breach of confidentiality can significantly impact various parties involved. For individuals, it can lead to loss of employment, damage to their professional reputation, and even legal issues. Organizations face reputational damage, loss of customer trust, and potential financial losses. Stakeholders, including investors, clients, and partners, can suffer from the breach, losing confidence in the organization and its ability to handle sensitive information responsibly.
Examples of Reputation Damage from Confidentiality Breaches
Numerous examples illustrate the devastating impact confidentiality breaches can have on reputation. A company’s image can be severely tarnished when confidential customer data is exposed, leading to a loss of trust and potentially impacting future business opportunities. The disclosure of sensitive financial information or trade secrets can also result in significant financial losses and reputational damage for an organization.
Furthermore, individuals who violate confidentiality agreements may face damage to their careers and professional standing, making it difficult to find future employment.
Steps to Take After a Potential Confidentiality Breach
In the event of a potential confidentiality breach, swift action is crucial. Immediately assess the extent of the breach, identify the affected parties, and document all relevant information. This documentation should include details about the nature of the breach, the individuals involved, and any potential damages. Consult with legal counsel to understand the specific implications of the breach and to develop a plan to mitigate the harm.
Implementing measures to prevent future breaches is equally important.
Reporting Procedures for Confidentiality Breaches, Cima ethics confidential information
Clear reporting procedures are essential for handling confidentiality breaches effectively. Organizations should establish a dedicated reporting channel for confidential information breaches, outlining the process for reporting such incidents. These procedures should include clear guidelines on who to contact, the information to be provided, and the expected response time. Following these established procedures helps in addressing the breach effectively and minimizing potential harm.
Establishing a secure and confidential reporting channel ensures that breaches are reported promptly and handled appropriately.
Case Studies and Examples
Navigating ethical dilemmas surrounding confidential information is crucial in today’s interconnected world. Real-world case studies provide invaluable insights into how professionals and organizations have faced these challenges, and how they’ve either succeeded or stumbled in upholding ethical standards. Analyzing these situations allows us to identify common pitfalls and develop strategies for better handling confidential data in the future.Understanding the ethical considerations in these cases isn’t just about avoiding penalties; it’s about maintaining trust, fostering a positive work environment, and upholding the integrity of the profession.
This section explores several examples, examining the factors contributing to breaches, and highlighting successful strategies for protecting sensitive information.
Real-World Case Studies
Numerous industries have faced ethical dilemmas involving confidential information. These range from breaches in healthcare to data leaks in finance, and the impact can be widespread and damaging. Examining these situations provides valuable lessons for protecting sensitive data and maintaining ethical standards.
- The Pharmaceutical Data Breach: A major pharmaceutical company experienced a data breach affecting patient records. The breach compromised sensitive information, including medical histories, diagnoses, and treatment plans. Ethical considerations included the potential harm to patient privacy, the legal implications of the breach, and the reputational damage to the company. The company’s response involved notifying affected individuals, implementing enhanced security measures, and cooperating with regulatory bodies.
Factors contributing to the breach could include outdated security systems, inadequate employee training, or insufficient monitoring of network activity. The company’s handling of the situation and the lessons learned included the importance of proactive security measures, transparent communication, and rigorous data protection policies.
- The Financial Reporting Scandal: A financial firm engaged in fraudulent accounting practices, concealing significant losses and manipulating financial reports to maintain a positive image. Ethical considerations centered on the firm’s fiduciary duty to its investors, the potential harm to the wider financial system, and the erosion of trust in the market. This case highlights the devastating consequences of unethical behavior and the importance of robust internal controls and independent audits.
Factors that contributed to the breach could include a lack of oversight, pressure to meet financial targets, and a culture that prioritized profits over ethics. The firm’s response and subsequent lessons learned involved significant penalties, reputational damage, and the implementation of stricter regulatory compliance.
Analyzing Factors Contributing to Breaches
Understanding the root causes of confidentiality breaches is crucial for prevention. These factors often overlap and interact in complex ways, leading to compromised data. Examining these factors helps to identify potential vulnerabilities and implement targeted solutions.
- Inadequate Security Measures: Outdated or insufficient security measures, such as weak passwords, insecure networks, and lack of access controls, can expose confidential information to unauthorized access. A critical factor in preventing these breaches is consistently upgrading security protocols and ensuring staff are aware of and follow proper security procedures.
- Human Error: Employee negligence, such as sharing passwords, failing to follow security protocols, or falling victim to phishing attacks, can lead to breaches. Education and training on cybersecurity awareness and safe practices are essential to mitigating the risk of human error.
- Malicious Actors: Cybercriminals and hackers can exploit vulnerabilities to gain unauthorized access to confidential information. Implementing robust security measures and employing proactive cybersecurity strategies are essential to protecting against these threats.
Lessons Learned
Analyzing past cases provides valuable lessons about safeguarding confidential information. Understanding these lessons allows for a proactive approach to ethical dilemmas and helps build a culture of confidentiality.
| Case Study | Key Lessons Learned |
|---|---|
| Pharmaceutical Data Breach | Prioritize proactive security measures, invest in employee training, and maintain transparent communication. |
| Financial Reporting Scandal | Implement strong internal controls, prioritize ethical conduct, and foster a culture of accountability. |
Future Trends in Protecting Confidential Information
The landscape of data protection is constantly evolving, driven by technological advancements and global regulatory pressures. Staying ahead of these changes is crucial for organizations to maintain the trust of stakeholders and avoid costly breaches. This section explores emerging trends in safeguarding confidential information, emphasizing the pivotal role of technology and international regulations.
Data Protection and Confidentiality: Predictions
The future of data protection will likely be characterized by a greater emphasis on proactive measures rather than simply reacting to breaches. Organizations will increasingly adopt a holistic approach to data security, encompassing not only technical safeguards but also robust policies and employee training programs. This shift reflects the understanding that human error and malicious intent are significant contributors to data breaches.
A focus on data minimization, coupled with strong access controls, will become paramount.
Emerging Technologies for Safeguarding Confidential Information
Several technologies are poised to reshape the way confidential information is protected. These include:
- Advanced Encryption Techniques: Quantum-resistant encryption methods will likely gain traction, as current encryption standards may become vulnerable to advancements in quantum computing. This proactive approach will be essential to safeguarding sensitive data from future threats.
- AI-powered Threat Detection: Artificial intelligence algorithms can analyze vast datasets to identify anomalies and potential threats in real-time. This allows for faster detection and response compared to traditional security methods. For instance, AI can detect unusual access patterns, suspicious email activity, or unusual file transfers.
- Blockchain Technology: Blockchain’s inherent immutability and transparency can be utilized to enhance data integrity and audit trails. This is particularly relevant for industries handling sensitive financial or healthcare information. Examples include secure supply chain management and verifiable identities.
- Zero Trust Security: The concept of zero trust mandates verification for every user and device accessing data, regardless of location or network. This approach significantly reduces the attack surface by requiring constant authentication, thus preventing unauthorized access.
The Role of Artificial Intelligence in Protecting Confidential Information
Artificial intelligence (AI) is not just a tool for identifying threats; it can also be a powerful asset in protecting confidential information. AI-driven systems can automate tasks like data masking, access control, and data loss prevention. Furthermore, AI can predict potential vulnerabilities and recommend preventative measures, enabling proactive security management.
Implications of Global Data Regulations on Confidential Information
Global data regulations, such as GDPR (General Data Protection Regulation) and CCPA (California Consumer Privacy Act), will continue to exert a significant influence on confidentiality practices. Organizations operating across borders must ensure compliance with diverse regulatory frameworks. These regulations are not just compliance mandates; they are indicators of evolving societal expectations regarding data privacy.
Potential Impact of Future Trends on Confidentiality Practices
| Trend | Potential Impact on Confidentiality Practices ||———————————————|—————————————————————————————————————————————————————————————————————–|| Advanced Encryption Techniques | Enhanced security against future threats, but also the need for ongoing updates and adaptation to new vulnerabilities.
|| AI-powered Threat Detection | Improved threat detection and response capabilities, potentially leading to a more proactive security posture.
However, concerns about bias in algorithms and potential misuse need to be addressed. || Blockchain Technology | Enhanced data integrity and audit trails, leading to greater transparency and trust, but also complexities in implementation and potential scalability issues.
|| Zero Trust Security | Reduced attack surface and increased security, but also increased administrative overhead and potential for friction in user experience.
|| Global Data Regulations | Increased costs associated with compliance, but also the potential for improved data protection standards and enhanced consumer trust.
|
Final Summary
In conclusion, maintaining CIMA ethics confidential information requires a strong understanding of the principles, procedures, and potential consequences. This guide has provided a comprehensive overview, from defining the core concepts to exploring future trends. By understanding the ethical and practical aspects of confidential information management, CIMA members can navigate the complexities of the modern business world with confidence and integrity.
Remember, safeguarding confidential information is not just a professional obligation, but a critical aspect of building trust and maintaining a strong reputation.