
No Global Tax Deal This Year, OECD Says
No global tax agreement this year oecd says – No global tax agreement this year, OECD says, leaving a void in international tax policy. This significant announcement from the Organisation for Economic Co-operation and Development (OECD) highlights the complexities and disagreements surrounding global tax reform. The failure to reach a consensus on a unified approach could have far-reaching implications for governments, corporations, and individuals worldwide. What specific issues stalled the negotiations?
What alternative approaches might be considered?
The OECD’s statement Artikels the key reasons behind the failure, including persistent disagreements on specific tax provisions and differing national priorities. This lack of agreement could lead to a variety of economic and social consequences, impacting international trade and investment. The global tax landscape remains uncertain, and the absence of a coordinated approach raises questions about the future of international tax policies.
Overview of the OECD Announcement
The Organisation for Economic Co-operation and Development (OECD) has announced the absence of a global tax agreement this year. This marks a significant setback in efforts to establish a more equitable and comprehensive global tax system. The lack of consensus highlights the complexities and deep-seated disagreements among participating nations.The failure to reach an agreement reflects a complex interplay of national interests, differing economic structures, and varying levels of political will.
Negotiations have been challenging, with key sticking points preventing a unified front. The implications for governments, corporations, and individuals are substantial and warrant careful consideration.
Reasons for the Failure to Reach an Agreement
The absence of a global tax agreement this year stems from several crucial factors. Disagreements on the specific tax rates and mechanisms for implementation were significant obstacles. Some nations prioritized their domestic interests over a globally unified approach, while others were concerned about the potential economic consequences of certain proposals.Furthermore, the varying capacities and priorities of different jurisdictions played a role in the negotiation process.
Discover how cima ethics confidentiality rules has transformed methods in this topic.
These factors, combined with political sensitivities and the intricacies of international tax law, have ultimately led to a standstill.
Potential Impacts of the Decision
The failure to agree on a global tax deal has substantial implications for various stakeholders. Governments face challenges in maintaining fiscal stability and addressing revenue shortfalls, potentially leading to increased reliance on other tax sources or adjustments in domestic tax policies.Corporations, especially multinational enterprises, are faced with uncertainties about their tax obligations and the potential for increased regulatory scrutiny.
The absence of a global standard may lead to a patchwork of national tax regimes, potentially impacting their operational strategies and financial planning.Individuals, particularly those with international financial interests, may experience adjustments in their tax obligations depending on their country of residence and the tax policies adopted by their respective governments. The complexity of the issue requires careful consideration and potential adaptation by individuals to address potential changes.
Areas of Disagreement
The core disagreements preventing a consensus centered around several key aspects. Different countries had varying opinions on the specific tax rates for multinational corporations and how to implement them. Another significant point of contention involved the allocation of taxing rights for digital services and the determination of appropriate profits for global companies. Different countries had different views on the tax rates for multinationals.
Key Takeaways
- A global tax agreement was not reached this year due to significant disagreements on tax rates, implementation mechanisms, and the allocation of taxing rights.
- The failure to agree on a global standard will likely lead to a patchwork of national tax regimes, impacting governments, corporations, and individuals.
- National interests and political sensitivities, along with the complexities of international tax law, played a crucial role in preventing consensus.
- The absence of a global agreement creates uncertainty about the future of international taxation and may necessitate alternative solutions to address the challenges of taxing multinational corporations.
Historical Context of Global Tax Negotiations: No Global Tax Agreement This Year Oecd Says
The failure of the OECD to reach a global tax agreement this year underscores the persistent complexities and challenges in forging international consensus on tax policies. This failure isn’t unprecedented, revealing a long and often arduous history of global tax negotiations, marked by both progress and setbacks. Understanding this history is crucial to appreciating the current stalemate and potential future trajectories.The quest for global tax harmony is a multifaceted endeavor, intertwined with shifting economic landscapes and evolving political ideologies.
Previous attempts to standardize tax practices have often faced opposition from nations seeking to protect their economic interests, creating roadblocks to achieving universal agreements. The current impasse highlights the continued tension between global tax fairness and national sovereignty.
Evolution of Global Tax Agreements
Global tax agreements have a long and winding history, evolving significantly from early attempts at harmonization to the complex negotiations of today. Initial efforts focused on basic tax principles and avoiding double taxation, leading to bilateral agreements between countries. Over time, the scope broadened, encompassing multinational corporations and the challenges of digitalization. This evolution reflects the changing nature of international commerce and the need for more sophisticated and adaptable tax frameworks.
Turning Points and Milestones, No global tax agreement this year oecd says
Significant milestones in global tax negotiations reveal crucial turning points and illustrate the dynamic interplay between economic and political forces. The introduction of the Organisation for Economic Co-operation and Development (OECD) and its role in coordinating international tax standards marked a notable advancement. The development of specific tax treaties and protocols, designed to address cross-border issues, represent further steps toward international tax cooperation.
The growth of multinational corporations and the emergence of digital economies have added new layers of complexity to these negotiations.
Political and Economic Factors
The political and economic landscapes significantly impact global tax negotiations. National interests and competing priorities often create friction. Economic power dynamics can influence the negotiation process, with larger economies potentially wielding more leverage. Political ideologies, including differing perspectives on tax fairness and economic development, also contribute to the challenges of reaching consensus.
Timeline of Significant Events in Global Tax Discussions
- 1920s-1930s: Early efforts to establish international tax cooperation focused primarily on avoiding double taxation and simplifying cross-border transactions. These early efforts were limited by the political and economic context of the time, including the Great Depression.
- 1950s-1960s: The establishment of the OECD marked a crucial step towards coordinating international tax standards. This laid the groundwork for future agreements and cooperation among nations.
- 1980s-1990s: The rise of multinational corporations and globalization significantly complicated tax issues. This period witnessed the development of more sophisticated tax treaties to address cross-border issues.
- 2000s-Present: The digital economy brought new challenges, including the taxation of companies with global operations but minimal physical presence in any one nation. Discussions about digital taxation and the taxation of multinational corporations became central to negotiations.
The timeline illustrates the gradual evolution of the global tax landscape, highlighting the increasing complexity of the issues involved. The changing nature of international commerce and the emergence of new economic models have made achieving global tax consensus more challenging.
Potential Impacts and Implications
The OECD’s announcement of no global tax agreement this year signals a significant setback in the ongoing quest for a fairer and more equitable global tax system. This absence of a consensus has profound implications for various aspects of the global economy, ranging from international trade to tax fairness and national budgets. The lack of a unified approach will likely exacerbate existing disparities and potentially hinder future economic growth.
Economic Consequences for Different Countries
The absence of a global tax agreement will likely lead to differing economic outcomes for various countries. High-tax jurisdictions might experience a reduction in revenue as multinational corporations shift profits to lower-tax environments. This could impact government budgets, potentially affecting public spending on crucial sectors like healthcare and education. Conversely, low-tax countries may see an increase in corporate activity and investment, but this could be accompanied by social pressures to address the resulting income inequality.
Impact on International Trade and Investment Flows
The lack of a global tax agreement will almost certainly affect international trade and investment flows. Uncertainty surrounding tax regulations and potential double taxation could deter companies from engaging in cross-border activities. This could lead to a decrease in foreign direct investment, particularly in developing nations, which rely heavily on foreign capital for growth and development. Conversely, some countries might seek bilateral agreements to mitigate the negative impacts, but this approach may not achieve the same comprehensive solution as a global accord.
Future of Global Tax Policies
The current situation points to a potential divergence in global tax policies. Individual countries may adopt unilateral measures to address tax avoidance and increase their tax revenues. However, this approach carries the risk of creating a fragmented and inconsistent global tax system, potentially hindering international trade and cooperation. An alternative scenario involves further negotiations and discussions to achieve a consensus in the future.
Check what professionals state about global cfo survey rebuild revenue streams and its benefits for the industry.
History is replete with instances where international agreements were reached after protracted negotiations, and there is reason to believe this pattern may repeat itself.
Repercussions on Tax Fairness and Equity
The absence of a global tax agreement is likely to exacerbate existing disparities in tax fairness and equity across the globe. Multinational corporations, particularly those in high-growth sectors, might continue to benefit from tax havens, leading to a situation where profits are not fairly distributed or taxed based on the value they create. This could lead to social unrest in many countries and potentially hinder development efforts in nations that rely on equitable tax systems.
Potential Impacts on Various Regions
Alternative Approaches and Future Strategies

The recent failure to reach a global tax agreement highlights the complexities and sensitivities surrounding international tax policy. Navigating these complexities requires innovative approaches and a willingness to compromise. Different models for global taxation, each with its own strengths and weaknesses, need careful consideration. This section explores potential alternative approaches, future negotiation strategies, and the evolving role of international bodies in facilitating such agreements.Alternative approaches to global taxation are crucial to overcome the current stalemate.
The current system, while attempting to address global tax avoidance, faces challenges in achieving consensus. This necessitates exploring different models, considering their advantages and disadvantages, and ultimately, seeking compromises that can foster a more equitable and sustainable global tax regime.
Potential Alternative Approaches
A variety of approaches are being considered, from bilateral agreements to regional tax harmonization. Each approach has its own set of pros and cons, affecting the degree of participation, enforcement, and administrative burdens.
- Bilateral Tax Treaties: These agreements can establish specific tax rules and procedures between two countries, potentially leading to more manageable negotiations and faster implementation. However, their limited scope might not address the systemic issues of global tax avoidance.
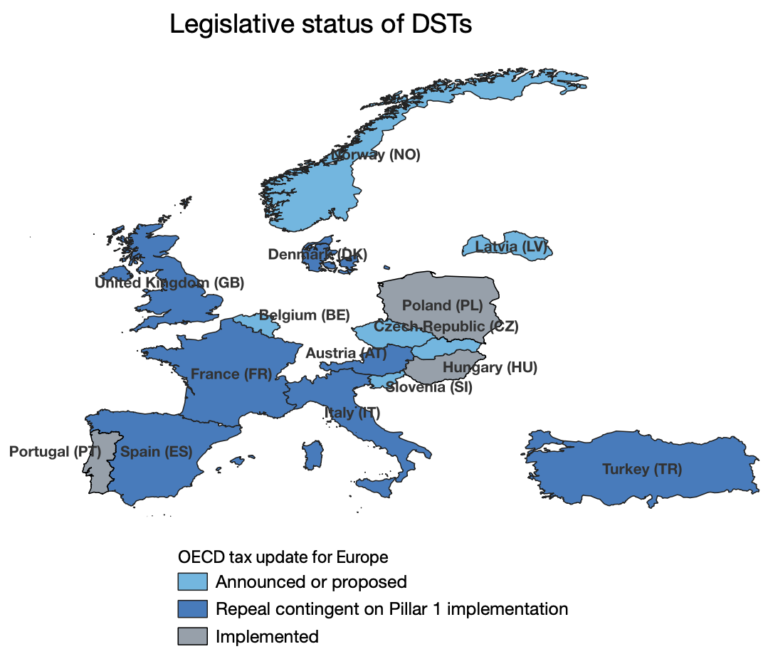
- Regional Tax Harmonization: Agreements within specific geographic regions, like the European Union, can provide a template for broader harmonization. This can address shared challenges and create a degree of consistency in tax policies across member states. However, regional approaches might not encompass the global scope of the problem, potentially creating a patchwork of differing regulations.
- Multilateral Tax Treaties: These agreements could encompass a wider range of countries, but the negotiation process is more complex and susceptible to gridlock. However, a well-structured agreement can establish a robust framework for global tax standards and create a more uniform tax environment.
Future Negotiation Strategies
Successful negotiation hinges on a flexible and adaptable approach. Different strategies can be employed to foster collaboration and address diverse perspectives.
Examine how finance departments evolving while bracing for coronavirus second wave can boost performance in your area.
- Phased Implementation: Instead of trying to achieve a comprehensive agreement immediately, a phased approach can focus on smaller, manageable areas of agreement. This could involve addressing specific tax avoidance practices or harmonizing certain tax rates gradually.
- Targeted Negotiations: Instead of trying to reach a global agreement at once, negotiators could focus on specific sectors or industries where tax avoidance is most prevalent. This targeted approach might be more manageable and could lead to tangible progress.
- Building Trust and Cooperation: Transparency, shared information, and mechanisms for dispute resolution are crucial. This will increase trust and facilitate future cooperation among nations.
Role of International Organizations
International organizations like the OECD play a critical role in fostering global tax cooperation. Their expertise and neutral platform are invaluable in facilitating discussions and developing frameworks for global tax standards.
- Facilitating Dialogue: International organizations can provide a platform for countries to discuss and debate different approaches to global taxation. This structured dialogue can lead to a better understanding of each country’s perspectives.
- Developing Standards: International organizations can help develop and disseminate best practices for tax administration, increasing transparency, and making it more difficult for multinational corporations to engage in tax avoidance.
- Providing Technical Assistance: International organizations can offer technical assistance to developing countries to help them strengthen their tax systems and enhance their capacity to collect taxes effectively.
Compromises and Concessions
Reaching a global tax agreement requires compromise and concessions from all parties. Specific concessions might involve a willingness to adjust tax rates or accept different enforcement mechanisms.
- Tax Rate Adjustments: Countries might be willing to accept a slight adjustment in their national tax rates to align with a global standard. This could be a necessary concession to achieve consensus.
- Enforcement Mechanisms: Different countries might agree on a shared enforcement framework, or possibly different enforcement mechanisms, to tackle tax avoidance effectively.
- Transparency and Information Sharing: Countries may be willing to share more tax information with one another, enhancing transparency and cooperation.
Comparing Different Approaches
Different approaches to global taxation each present unique advantages and disadvantages.
| Approach | Advantages | Disadvantages |
|---|---|---|
| Bilateral Treaties | Manageable negotiations, faster implementation | Limited scope, doesn’t address systemic issues |
| Regional Harmonization | Addresses shared challenges, consistency | Limited scope, potentially creating a patchwork of regulations |
| Multilateral Treaties | Robust framework, uniform tax environment | Complex negotiations, susceptible to gridlock |
Analysis of Stakeholder Perspectives
The OECD’s announcement of no global tax agreement this year has ignited a complex web of reactions from various stakeholders. Governments, corporations, and individuals hold differing perspectives on the implications of this outcome, each with their own justifications and potential repercussions. Understanding these varied viewpoints is crucial to assessing the future trajectory of global tax reform.The lack of a consensus highlights the inherent difficulties in forging international agreements on tax matters.
Diverse national interests and priorities, coupled with differing interpretations of economic principles, often lead to prolonged negotiations and compromises. This dynamic is particularly evident in the realm of global taxation, where the interests of governments, corporations, and individuals often clash.
Government Perspectives
Governments face a delicate balancing act. While some governments may favor a global tax agreement to address tax avoidance and raise revenue, others may prioritize national interests or concerns about the potential impact on their domestic economies. For example, a country with a strong reliance on corporate tax revenue might be hesitant to cede taxing authority to a global body, potentially impacting its fiscal capacity.
The political ramifications of such a decision can be significant.
Corporate Perspectives
Corporations often advocate for a streamlined and predictable global tax system. This preference stems from the desire to minimize compliance costs and avoid double taxation. However, corporations may also be concerned about the impact of increased tax burdens on their profitability and competitiveness. A lack of a global agreement might lead to a patchwork of national tax regimes, creating complexities in cross-border operations.
This could involve increased compliance costs and potential inconsistencies in tax rates across different jurisdictions.
Individual Perspectives
Individuals, particularly those with substantial financial resources, are impacted by the global tax landscape. A lack of global agreement could potentially lead to more complex tax filing procedures and potentially higher tax burdens, depending on national regulations. Increased complexity in tax compliance for individuals might involve more paperwork and professional assistance. Furthermore, the effectiveness of tax evasion measures for individuals could vary significantly based on national laws.
Potential for Future Conflicts and Disagreements
The absence of a global tax agreement this year could exacerbate existing tensions between governments and corporations, and even between individuals and governments. Disagreements regarding the allocation of taxing rights, the level of tax rates, and the implementation mechanisms could escalate. For example, nations with strong tax revenue needs might feel that corporations are unfairly avoiding taxes, leading to disputes over jurisdiction and the equitable sharing of revenue.
Table Comparing Stakeholder Perspectives
Illustrative Examples of Global Tax Policies
The global tax landscape is a complex web of agreements, treaties, and policies designed to manage cross-border transactions and revenue collection. Understanding how these policies have evolved and how they impact different economies is crucial for navigating the intricacies of international finance. This exploration will highlight various global tax policies, their effects, and their effectiveness.
Existing Global Tax Policies
Various international agreements and policies shape global tax systems. These policies aim to address issues like tax avoidance, base erosion, and ensuring a fair and equitable distribution of tax burdens. Key areas include multinational corporate taxation, transfer pricing rules, and international tax treaties. Understanding these policies requires a nuanced view of their impact on different economies and stakeholders.